Most cloud attacks do not start with a dramatic malware alert. They start with normal-looking behavior tied to the wrong identity, workload, or permission path. That is why contextual and entity-centric threat detection matters. Instead of treating every log as a separate event, it connects identities, assets, privileges, and attack paths into one story. For security teams, that means fewer low-value alerts, faster triage, and a clearer view of what actually puts sensitive cloud assets at risk. For organizations operating across AWS, Azure, and GCP, this approach is quickly becoming essential.
Key Takeaways
- Context matters more than raw alerts. A denied API call or unusual login is rarely useful on its own. It becomes useful when you know who triggered it, what they touched, and what they could reach next.
- Entities are the real unit of cloud detection. In cloud environments, identities, workloads, service accounts, and data stores change constantly. Detection needs to follow those entities, not just isolated events.
- Attack paths change prioritization. A medium-severity anomaly on a low-risk asset is not the same as the same anomaly on an identity that sits one step away from production data.
- Traditional SIEM-style rules miss too much context. Static detections struggle in environments where permissions, roles, containers, and APIs change by the hour.
- This is where modern CNAPP and ITDR strategies meet. Teams that can connect posture, identity, runtime, and relationships are in a far better position to catch real cloud threats early.
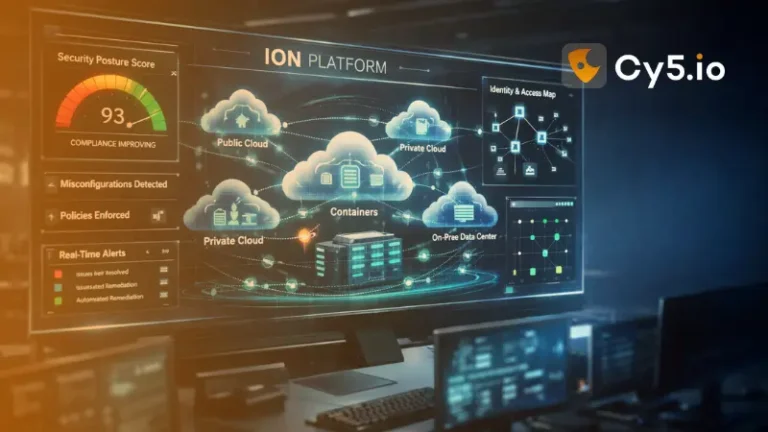
In cloud security, raw alerts are no longer enough, what matters is who did what, where, and why in real time. Contextual and entity‑centric threat detection shifts focus from isolated events to the behavior and relationships of identities, workloads, and resources across AWS, Azure, and GCP. This is where CNAPP, XDR, ITDR, and graph‑based analytics converge, and where platforms like Cy5’s ion Cloud Security are quietly redefining how modern teams detect and stop cloud attacks.
Who This Article Is For
This guide is for cloud security leaders, detection engineers, SOC teams, DevSecOps practitioners, and platform teams trying to answer a simple but increasingly urgent question: how do we separate real cloud threats from endless background noise?
If your team works across AWS, Azure, or GCP and deals with alert fatigue, identity risk, exposed attack paths, or unclear prioritization, this article will help. You will learn:
- what contextual and entity-centric threat detection actually means
- why traditional cloud detections fall short
- how attack paths and entity relationships improve signal quality
- where CNAPP, XDR, and ITDR fit in
- how platforms like Cy5’s ion Cloud Security help operationalize this approach
In cloud security, the problem is rarely a lack of data. The real problem is understanding which identity, permission path, or workload behavior actually changes your risk.
What Is Contextual & Entity‑Centric Threat Detection?
Contextual & entity‑centric threat detection is an approach that builds a continuously updated picture of every entity in your cloud, users, service accounts, IAM roles, workloads, APIs, data stores, and evaluates their behavior in the full context of identities, relationships, and risk. Instead of looking at an event like “API call denied” in isolation, it examines who triggered it, from which device and location, against what baseline, and where that entity sits in your cloud attack graph.
This approach answers questions like:
- Is this failed login from a service account normal for this time and location?
- Is this new API key suddenly reading sensitive S3 buckets it never touched before?
- Does this admin role’s behavior align with its historical access patterns?
By fusing signals from identity, posture, vulnerabilities, and runtime activity, contextual detection turns noisy telemetry into high‑fidelity stories about real threats, lateral movement, privilege escalation, insider abuse, and stealthy cloud‑native attacks.
Why This Matters More in 2026
Cloud environments are not just getting larger. They are getting harder to reason about. Identities are more distributed, machine accounts are multiplying, permissions are becoming harder to track, and attackers are getting better at blending into legitimate cloud activity.
That changes the job of threat detection. The challenge is no longer collecting enough data. Most teams already have too much data. The challenge is understanding which behavior matters, which entities are high risk, and which changes create real attack opportunities.
In 2026, cloud defense depends less on isolated alerts and more on connecting identity, behavior, and exposure into a single view.
Contextual Detection vs Traditional Detection
Traditional detection usually asks: did a rule fire?
Contextual detection asks: does this behavior make sense for this entity, in this environment, at this moment, given what it can reach next?
That difference sounds subtle, but in practice it is huge.
A traditional SIEM rule might flag five failed logins from one IP address. That is useful, but incomplete. It still leaves the analyst with basic questions:
- Was the identity high privilege or low privilege?
- Was this account used by a human or an automated pipeline?
- Has this behavior happened before?
- Is the account connected to sensitive assets?
- Did the same identity later assume a more privileged role?
Contextual detection fills in those blanks. It takes the raw event and places it inside the larger story. That is what helps analysts make faster, better decisions without chasing every low-context alert.
Why Traditional Threat Detection Fails in Cloud
Most organizations still rely on SIEM‑centric or signature‑driven detection patterns that were designed for static, perimeter‑based networks. Cloud environments break these assumptions in several ways.
Event‑Centric vs Entity‑Centric
Traditional detection treats each log line or alert as a self‑contained signal: a rule fires, an alert is generated, an analyst triages, and the process repeats. But in cloud, the same entity may:
- Assume multiple roles across accounts.
- Spin up and down dynamically as a container or serverless function.
- Interact with dozens of services within seconds.
Without an entity‑centric view, the system misses slow‑burn attacks and low‑and‑slow lateral movement that only make sense when you connect activity over time.
Lack of Context
A login from a new IP. An S3 permission change. A Kubernetes pod reading secrets.
Individually, these may be “low severity.” Combined, with the right context, they might indicate a compromised CI/CD pipeline or data exfiltration path. Traditional tools often lack:
- Business context (what data is stored where, which assets are crown‑jewels).
- Identity context (who can become what via role chaining).
- Relationship context (how identities, networks, and data stores connect).
Most cloud attacks do not announce themselves as attacks. They show up as small, legitimate actions connected in the wrong sequence.
Static Rules in a Dynamic World
Rule‑based detections lag behind attacker innovation and cloud platform changes. In fast‑moving environments, developers continuously create new roles, services, and APIs; static signatures can’t keep up. Behavioral and risk‑based approaches are needed to baseline “normal” and flag meaningful deviations without drowning teams in false positives.
Traditional vs Contextual vs Entity-Centric Detection

| Dimension | Traditional Detection | Contextual Detection | Entity-Centric Detection |
|---|---|---|---|
| Primary Focus | Individual log events and rule matches | Events enriched with identity, asset, and path context | Behavior and relationships of identities, workloads, and resources |
| Unit of Analysis | Log line or alert | Event + surrounding context | Entity across time and relationships |
| Strengths | Simple, fast to deploy, well understood | Adds business meaning, reduces noise | Tracks identity behavior, maps paths, detects slow-burn attacks |
| Weaknesses | High false positives, no relationship awareness | Depends on data quality and integration depth | Requires graph modeling and ML baselines |
| Cloud Suitability | Low — designed for static, perimeter-based networks | Medium-High — works well with cloud telemetry | High — built for dynamic, identity-driven cloud environments |
| False Positive Risk | High | Medium | Low |
| Best Use Case | Known pattern matching in stable environments | Prioritizing alerts by business impact | Detecting lateral movement, privilege escalation, identity compromise |
Entities: The Building Blocks of Modern Detection
To understand entity‑centric detection, you need a clear mental model of what counts as an “entity” in cloud security.
Types of Entities in Cloud
Typical entity categories include:
- Human identities: Users, admins, contractors in IAM or IdPs.
- Machine identities: Service accounts, IAM roles, Kubernetes service accounts, workload identities.
- Compute: EC2 instances, VMs, containers, pods, serverless functions.
- Data stores: S3 buckets, Blob storage, databases, data lakes.
- Network constructs: VPCs, subnets, security groups, load balancers.
- Secrets & keys: API keys, tokens, certificates, KMS keys.
- SaaS & APIs: Third‑party integrations and their tokens.
Each entity has attributes (role, tags, environment, sensitivity, typical access patterns) that define its baseline and risk.
Entity Behavior Analytics (UEBA for Cloud)
User and Entity Behavior Analytics (UEBA) for cloud tracks how entities usually behave, which APIs they call, which resources they access, from where and when, and then highlights anomalies. Examples:
- A CI/CD role suddenly making interactive console calls.
- A storage account being accessed from a geography it has never seen before.
- A Kubernetes pod reaching out to external domains unrelated to its service.
This behavior‑first view is the foundation of entity‑centric detection.
What This Looks Like in Practice
Imagine a developer account signs in from a new location. On its own, that might be harmless. People travel. VPNs change. IPs shift.
Now add a little more context:
- the account has not logged in for two weeks
- it immediately assumes a production role it rarely uses
- that role changes a security group
- minutes later, it reads from a sensitive storage bucket
None of those actions are necessarily catastrophic in isolation. Together, they form a credible attack story. That is exactly the kind of pattern contextual and entity-centric detection is designed to catch.
Where CNAPP, XDR, and ITDR Start to Overlap
One reason this topic is gaining attention is that it sits in the middle of several important security categories.
- CNAPP gives teams visibility into cloud posture, identity exposure, workload risk, and attack paths.
- XDR helps correlate incidents across endpoints, cloud, identity, and network activity.
- ITDR focuses on the abuse of identities, sessions, entitlements, and trust relationships.
In real-world environments, cloud attacks often touch all three. A compromised identity may start in an IdP, pivot through cloud permissions, touch a workload, and move toward sensitive data. Teams need a way to connect those signals without forcing analysts to manually stitch them together.
That is where contextual, entity-centric detection becomes especially valuable.
Security teams do not need more alerts. They need fewer alerts with enough context to make a decision.
What Makes Detection “Contextual”?
Contextual detection enriches events with additional signals so you can distinguish harmless anomalies from real attacks.
Types of Context
Key context dimensions include:
- Identity context: Privilege level, group membership, role trust relationships, MFA status, history of role assumptions.
- Asset context: Environment (prod/test), data sensitivity, exposure (internet‑facing or internal), criticality to the business.
- Relationship context: Graph of which identities can access which assets and via which paths (e.g., role chaining, trust policies, network links).
- Threat context: MITRE ATT&CK mapping, known malware or TTPs, threat intel tags.
- Temporal context: Time of day, sequence of events, long‑running vs bursty activity patterns.
Anatomy of a Cloud Attack Path

Compromised Identity
Role Chaining
Misconfiguration Exploit
Lateral Movement
Sensitive Data Access
Exfiltration Opportunity
Contextual Risk Scoring
Rather than scoring each event in isolation, contextual detection engines calculate risk at the entity and path level. For instance:
- A medium‑severity anomaly on a low‑privilege dev account might be low risk.
- The same anomaly on an identity that sits on an attack path to a payment database is high risk.
Contextual risk scoring helps triage which alerts require immediate action and which can be monitored.
What an Entity Graph Actually Gives You
The term “entity graph” can sound abstract, but the idea is practical. It is a living map of your cloud environment that shows how identities, workloads, resources, permissions, and data stores connect to each other.
That matters because attackers do not think in log lines. They think in paths.
They look for:
- trust relationships they can abuse
- permissions they can inherit
- workloads they can pivot through
- data stores they can reach
- controls they can weaken along the way
An entity graph gives security teams that same path-based perspective. Instead of asking, “Was this event strange?” teams can ask, “What does this event make possible now?”
How Contextual & Entity‑Centric Detection Works
Under the hood, most modern implementations follow a lifecycle similar to advanced CNAPP, XDR, and ITDR solutions.
Data Collection Across Cloud and Identity
The engine ingests telemetry from:
- Cloud providers (CloudTrail, Azure Activity Logs, GCP Audit Logs).
- Identity providers (Azure AD, Okta, IAM).
- Workloads and containers (Kubernetes audit logs, EDR/XDR).
- SaaS and security tools (SIEM, vulnerability scanners, CSPM, CIEM).
This data is normalized into a unified schema where events are anchored to entities instead of log sources.
Building an Entity Graph
Entities and their relationships are modeled as a security knowledge graph. Each node represents an entity; edges represent permissions, trust, network paths, or data flows. This enables graph‑based threat detection such as:
- Shortest paths from an external IP to a sensitive S3 bucket.
- All roles that can indirectly become a powerful admin.
- Clusters of entities frequently used together in suspicious sequences.
Behavior Baselines and Anomaly Detection
Machine learning models build baselines of normal behavior per entity and per peer group. They then flag:
- Unusual resource access (new buckets, new databases).
- Divergent API usage (privilege escalation APIs, policy changes).
- Abnormal communication patterns between workloads.
These anomalies are enriched with graph context before being turned into alerts.
Multi‑Signal Correlation and Story Building
Instead of generating a separate alert per anomaly, contextual detection correlates multiple signals into a single “attack story.” For example:
- Developer identity logs in from a new location.
- Same identity assumes a high‑privilege role not used in months.
- That role modifies a security group and reads a sensitive data store.
Together, this becomes a high‑confidence incident of potential account takeover and data exfiltration.
From Raw Telemetry to Prioritized Incident

Where CNAPP, XDR, and ITDR Converge
“Contextual & entity‑centric threat detection” sits at the intersection of CNAPP, cloud XDR, and ITDR.
CNAPP: Cloud‑Native Application Protection Platform
CNAPP unifies CSPM, CWPP, CIEM, and exposure management into one cloud‑native platform. When CNAPPs embed contextual, entity‑centric detection, they can:
- Correlate misconfigurations, vulnerabilities, and identity risks with runtime behavior.
- Flag not just unsafe posture, but live threat activity along real attack paths.
- Prioritize remediation based on both posture and behavioral risk.
XDR and Cloud XDR
XDR extends detection beyond endpoints to identity, network, email, and cloud. Cloud XDR capabilities bring cloud telemetry into this picture so that:
- Cloud anomalies are correlated with endpoint and identity events.
- Entity‑centric threat stories span on‑prem, SaaS, and multi‑cloud.
- Response playbooks can contain and remediate across domains.
ITDR: Identity Threat Detection & Response
Identity is now a primary attack surface. ITDR focuses specifically on detecting compromised identities, abuse of trust relationships, and privilege escalation paths. Entity‑centric detection is a natural foundation for ITDR because it continuously evaluates:
- Identity behavior against baselines.
- Risky role chains and delegated access.
- Signals of credential theft and session hijacking.
CNAPP vs XDR vs ITDR vs SIEM

| Platform | Core Purpose | Data Sources | Best For | Blind Spots |
|---|---|---|---|---|
| CNAPP | Unified cloud posture, workload, identity, and exposure management | Cloud APIs, IAM, CSPM, CWPP, CIEM | Cloud-native risk prioritization and attack path analysis | Limited endpoint and on-prem network visibility |
| XDR / Cloud XDR | Cross-domain detection and response | Endpoints, cloud, identity, network, email | Correlated detection across hybrid environments | Often shallow on cloud-native posture and identity graphs |
| ITDR | Identity-focused threat detection and response | IdP, IAM, session and token activity | Detecting credential theft, privilege escalation, identity abuse | Limited view of workloads, posture, and data-layer risk |
| SIEM | Log aggregation, correlation, and compliance | All log sources ingested | Broad log retention, rule-based correlation, compliance reporting | Lacks graph context, identity baselines, and cloud-native enrichment |
Key Use Cases for Contextual & Entity‑Centric Detection
This approach unlocks several high‑value detection and response use cases for cloud‑first organizations.
Early Detection of Identity Compromise
By tracking identity anomalies and risky entity graphs, teams can detect:
- Credential stuffing and password spraying attempts against cloud logins.
- OAuth and token abuse for cloud and SaaS apps.
- Suspicious role assumptions that pivot toward admin or data‑heavy roles.
These signals often appear long before a full‑blown breach is obvious in logs.
Lateral Movement and Privilege Escalation in Cloud
Contextual detection can visualize and flag:
- Lateral movement between workloads and accounts via trusted relationships.
- Abuse of IAM misconfigurations to escalate privileges.
- Use of living‑off‑the‑cloud techniques (legitimate APIs used maliciously).
Rather than waiting for exfiltration, teams can intervene at the first signs of suspicious path traversal.
Insider Threat and Abuse of Legitimate Access
Insiders and compromised insiders often operate within permitted access boundaries but exhibit unusual behavior patterns. Entity‑centric analytics identifies:
- Access to sensitive resources outside typical hours or projects.
- Large, unexpected data reads from critical buckets.
- Attempts to disable logging, alerts, or security controls.
Contextual risk scoring helps separate legitimate urgent maintenance from abuse.
Detection Engineering and Threat‑Informed Defense
For detection engineering teams, contextual telemetry and entity graphs make it easier to:
- Map detections to MITRE ATT&CK techniques and cloud‑specific TTPs.
- Build high‑fidelity, low‑noise correlations across multiple signals.
- Continuously tune detections based on real attacker behavior and purple‑team exercises.
Why Attack Path Analysis Changes Prioritization
Most security teams already have a long list of findings. Misconfigurations, risky identities, exposed assets, unusual behavior, excessive permissions. The hard part is deciding what matters first.
Attack path analysis helps by adding consequence to the conversation.
A low-priority issue can become urgent if it sits on a short path to a critical asset. On the other hand, a technically severe finding may be less important if it is isolated and hard to exploit in practice.
This is one of the biggest advantages of combining contextual detection with cloud relationship mapping. You are not just seeing what is wrong. You are seeing what could be reached, how quickly, and by whom.
See how Cy5 maps cloud attack paths across AWS, Azure, and GCP.
Explore ion Cloud SecurityAI‑Native Threat Detection and Security Knowledge Graphs
AI‑native detection doesn’t mean throwing a generic model at logs. It means using graph‑aware, context‑rich models designed for the structure and scale of cloud environments.
Security Knowledge Graph for Threat Detection
A security knowledge graph ties together:
- Entities and their attributes.
- Relationships and trust paths.
- Historical behavior and anomalies.
- Threat intel, ATT&CK mapping, and detection logic.
Graph‑based threat detection uses algorithms like shortest path, community detection, and centrality to identify high‑risk entities and attack paths that warrant focused monitoring.
AI Contextual Risk Scoring
AI models can dynamically adjust risk scores based on:
- Recent changes in posture (new misconfigurations, exposed assets).
- Shifts in behavior (unusual login sources, new resource combinations).
- Global trends (new campaigns targeting specific cloud services).
This produces AI‑powered cloud threat detection that is adaptive, context‑aware, and aligned with real‑world attack patterns rather than static thresholds.
What to Look For in a Contextual Threat Detection Platform
Not every tool that claims “AI-driven” or “context-aware” detection actually delivers what security teams need. When evaluating a platform, the practical questions are more important than the category label.
Look for a solution that can:
- connect identity, asset, posture, and runtime signals
- build live relationships across AWS, Azure, and GCP
- show attack paths, not just findings
- baseline both human and machine behavior
- prioritize based on exploitability and business impact
- reduce alert volume through strong correlation
- support investigations with understandable incident narratives
- fit into existing SIEM, XDR, and response workflows
If a platform can detect anomalies but cannot explain why they matter, analysts still end up doing the hard work manually.
Why This Also Matters for Compliance
Contextual detection is not just useful for incident response. It also gives security leaders a more defensible compliance story.
Auditors and regulators increasingly expect organizations to show more than checkbox controls. They want evidence that high-risk identities, sensitive assets, and meaningful exposure paths are being monitored continuously.
That is where contextual, risk-based monitoring becomes helpful. Instead of saying, “We collect logs,” teams can say, “We monitor the identities and assets most likely to drive real business risk, and we prioritize the paths an attacker would actually use.”
For compliance-minded organizations, that is a much stronger position.
How Contextual Detection Supports Key Frameworks

| Framework | Relevant Control Area | How Contextual Detection Helps |
|---|---|---|
| SOC 2 | Monitoring, access control, risk assessment | Continuous identity and entity monitoring tied to business-critical assets |
| ISO 27001 | Access management, incident detection, information classification | Risk-based detection aligned to classified assets and identity trust paths |
| NIST CSF | Identify, protect, detect, respond | Entity graph mapping for asset identification, behavioral baselines for detection |
| GDPR | Data protection, breach notification, access monitoring | Tracks access to personal data stores and surfaces unauthorized data-path activity |
| PCI DSS | Privileged access, logging, monitoring | Contextual monitoring of privileged identities accessing cardholder data environments |
How ion Cloud Security Delivers Contextual & Entity‑Centric Detection
Cy5’s ion Cloud Security platform is built as a CNAPP with deep emphasis on cloud relationship mapping, attack path visualization, and AI‑driven risk prioritization across AWS, Azure, and GCP. Its design naturally supports contextual and entity‑centric threat detection without adding operational drag for security and DevSecOps teams.
Unified Multi‑Cloud Entity Graph
ion continuously discovers more than 100 resource types across public clouds and automatically builds a live entity graph connecting identities, workloads, data stores, and configurations. This graph is the backbone for:
- Enhanced threat path visualization to show how attackers could traverse your environment.
- Entity risk scoring that factors in both posture and behavioral context.
- Real‑time visibility into new entities and relationships as they appear.
For security leaders, this means you’re not guessing where your real exposure lies, you can see it.
Real‑Time Cloud Threat Detection with Context
ion ingests cloud logs, identity events, and posture signals, then correlates them at the entity level. Its detection logic:
- Baselines behavior for human and machine identities.
- Flags anomalous activity along known attack paths.
- Elevates incidents where anomalies intersect high‑value assets.
Instead of endless low‑context alerts, teams receive narrative‑style incidents with clear “who/what/where/how” grounded in actual cloud relationships.
Risk‑Based Prioritization and Automated Compliance
ion doesn’t treat all misconfigurations or anomalies equally. It uses contextual risk scoring to highlight:
- Entities that sit on critical attack paths.
- Behavior changes that meaningfully increase blast radius.
- Compliance gaps that directly translate into exploitable exposure.
With prebuilt templates for frameworks like SOC 2, ISO 27001, NIST, and GDPR, ion helps you prove not just control coverage, but active risk management in line with regulators’ expectations.
Built for Speed: Agentless and Cloud‑Native
Because ion is agentless and cloud‑native, organizations can:
- Onboard accounts quickly and see contextual detection in action within minutes.
- Avoid complex deployment projects and agent sprawl.
- Scale detection across multi‑cloud without re‑architecting security infrastructure.
For fast‑moving engineering teams, this “observe more, install less” model reduces resistance and accelerates adoption.
Why Cy5’s ion Cloud Security Platform is Well Suited to this Approach
A lot of tools can collect cloud findings. Fewer tools can turn those findings into a useful picture of exposure and active risk.
That is where CY5’s ion Cloud Security stands out.
ion is designed to help teams see how cloud entities actually relate to each other across AWS, Azure, and GCP. Instead of forcing analysts to jump between posture alerts, identity logs, and disconnected dashboards, it helps connect the dots:
- which identities matter most
- which workloads and resources they can reach
- which attack paths are currently exposed
- which behavior changes increase real risk
- which incidents deserve immediate attention
For teams dealing with multi-cloud complexity, alert fatigue, and pressure to justify remediation priorities, that kind of context is not just helpful. It is operationally necessary.
Key Metrics After Adoption

Why Deployment Speed Matters More Than People Admit
Security teams often know they need better visibility, but they hesitate because they assume deployment will be long, disruptive, or resource-heavy.
That is one reason the operational model matters. A cloud-native, agentless approach lowers friction. Teams can get visibility faster, reduce rollout resistance, and start mapping risk without launching a long infrastructure project first.
In practice, that means less time spent planning deployment and more time spent understanding what is actually exposed.
Want to see which identities and attack paths actually matter in your cloud environment?
Explore how Cy5’s ion Cloud Security helps teams map relationships, prioritize exposure, and reduce low-context cloud alerts.
Implementing Contextual & Entity‑Centric Detection in Your Org
Shifting to contextual and entity‑centric detection is both a technology and operating‑model change.
Start with Identity and Crown‑Jewel Assets
Identify:
- Your most critical identities (admins, CI/CD, production service accounts).
- Your crown‑jewel assets (PII stores, payment systems, control planes).
Use a platform like ion to map attack paths and entity relationships around these entities first, so early wins tie directly to business risk.
Integrate Telemetry and Break Silos
Ensure you are ingesting:
- Cloud audit logs from all providers.
- Identity and access logs from IAM and IdPs.
- Posture, vulnerability, and exposure findings from CSPM and CIEM.
The more complete the entity view, the more accurate contextual detection becomes.
Tune for Your Environment and ICP
Your risk model should reflect your business:
- BFSI and regulated industries may prioritize data exfiltration and insider threats.
- SaaS and digital‑native businesses may focus on CI/CD compromise and abuse of machine identities.
Align detection policies, baselines, and response playbooks with those priorities to reduce noise and increase relevance.
Embed into Detection Engineering and DevSecOps
Use contextual detections and entity graphs as inputs for:
- Threat modeling and purple‑team exercises.
- Detection engineering backlogs mapped to ATT&CK.
- “Security as code” pipelines that block risky changes before production.
Over time, contextual detection becomes part of how your teams design, build, and operate cloud services — not just a dashboard they check during incidents.
Why This Topic Matters Now (2026–2027 Lens)
Cloud and AI security are converging rapidly, and attackers are already exploiting gaps in identity and context. Industry studies show:
- A growing share of cloud breaches start from identity misuse and lateral movement rather than pure perimeter flaws.
- A single misconfigured asset can now create hundreds or thousands of potential attack paths in large environments.
- Exposure management and attack path analysis are becoming must‑have capabilities, not nice‑to‑have add‑ons.
Contextual & entity‑centric detection is emerging as the response to this reality, and organizations that adopt it early will not only reduce breach risk, but also set a defensible, modern security narrative for customers, regulators, and boards.
Conclusion
Cloud attacks are getting harder to spot because they increasingly look like ordinary activity. A login, a role assumption, a policy change, a data read. None of these actions is automatically malicious. The danger appears when they happen in the wrong sequence, through the wrong identity, along the wrong path.
That is why contextual and entity-centric threat detection matters. It gives security teams a way to understand behavior in relation to exposure, relationships, and business impact. It replaces isolated alerts with usable attack stories.
For modern cloud security programs, that shift is becoming less of an innovation and more of a requirement. And for teams that need to operationalize it across AWS, Azure, and GCP, platforms like Cy5’s ion Cloud Security can help turn that model into day-to-day practice.
If your team is still chasing isolated cloud alerts, it may be time for a different model.
If your team is still chasing isolated cloud alerts, it may be time for a different model. Book a demo of Cy5’s ion Cloud Security to see how contextual, entity-centric detection can help you connect identity, exposure, and attack paths across AWS, Azure, Oracle, and GCP.
FAQs: Contextual & Entity‑Centric Threat Detection, CNAPP, and ion Cloud Security
Contextual threat detection in cloud security is the process of evaluating security events in light of who generated them, what they touched, how they relate to other entities, and how they map to real attack paths. Instead of firing a rule for every suspicious log line, it builds rich, context‑aware alerts that reflect actual risk to your business.
Entity‑centric security is a strategy that models and protects your environment around entities, identities, workloads, data stores, rather than IPs or static hosts. Each entity gets a behavioral baseline, risk score, and relationship map, so you can detect attacks as changes in how entities act and connect. This approach is particularly effective in dynamic, cloud‑native infrastructures.
Traditional SIEM rules usually match patterns in logs (e.g., “five failed logins in a minute from one IP”) without deep awareness of entity history, graph relationships, or business impact. Contextual detection enriches those events with identity, asset, and path context and then uses that composite picture to decide whether something is benign or dangerous. The result is fewer, higher‑quality alerts and richer stories for analysts.
UEBA (User and Entity Behavior Analytics) is a foundational component of contextual detection because it establishes baselines for how entities usually behave. Entity‑centric detection systems use UEBA to spot anomalies, then add graph and risk context to determine if those anomalies matter. Think of UEBA as “what changed” and contextual detection as “why it matters.”
Entity risk scoring assigns a dynamic risk value to each identity, workload, or resource based on its privileges, relationships, posture, and behavior over time. For example, a CI/CD service account that sits on multiple attack paths to production databases and shows unusual API usage will receive a high risk score. This helps teams focus on protecting and monitoring the entities that matter most.
By combining signals from multiple sources and adding rich context, contextual detection suppresses alerts that look unusual but are harmless and elevates those that are part of real attack narratives. For instance, a single odd login might be ignored if the entity’s overall behavior remains normal and sits far from sensitive paths. On the other hand, a small anomaly on a high‑risk entity near crown‑jewel assets is treated as a priority incident.
Graph modeling maps entities and their relationships, such as permissions, trust, and network connectivity. This model enables detection engines to understand how an attacker could move through your environment and which entities are structurally important. When anomalies occur on or near key nodes or edges in this graph, they are treated with higher urgency because they can quickly open paths to critical assets.
ITDR (Identity Threat Detection & Response) focuses specifically on threats that target or abuse identities — phishing, token theft, privilege escalation, and abuse of entitlements. Contextual & entity‑centric detection provides the data, baselines, and graph context ITDR needs to distinguish normal identity use from malicious behavior. Together, they reduce the time from identity compromise to detection and response.
Yes. In fact, multi‑cloud and hybrid complexity is one of the main reasons this approach is gaining traction. By building a unified entity graph across AWS, Azure, GCP, and on‑prem identity and workloads, contextual detection systems can trace threats that hop between providers or from on‑prem to cloud. Platforms like ion are designed specifically to unify and normalize telemetry across these environments.
ion Cloud Security discovers cloud resources and identities, builds a cloud relationship graph, baselines behavior, and then correlates logs, posture, and vulnerability data at the entity level. Its threat path visualization shows how anomalies and misconfigurations intersect on real attack paths to critical assets. Automated, contextual risk scoring then surfaces the entities and incidents that deserve immediate focus.
ion is primarily a CNAPP‑style cloud security and exposure management platform that can complement, and in some cases offload, cloud‑specific detection tasks from SIEM and XDR. Many organizations continue to use SIEM/XDR for broad log retention, endpoint, and network coverage while relying on ion for cloud‑native posture, attack paths, and contextual detection in AWS, Azure, and GCP. Integration options allow sharing incidents and context between these layers.
Contextual & entity‑centric detection gives you concrete, defensible evidence that you are monitoring identities, critical assets, and attack paths in a risk‑based way. This aligns well with modern expectations in frameworks like SOC 2, ISO 27001, and NIST, where regulators and auditors look for continuous, context‑aware monitoring rather than checkbox controls. ion’s prebuilt compliance templates help translate this into reports and dashboards auditors can understand.
Teams benefit from skills in cloud architecture, identity and access management, detection engineering, and basic data analysis. However, modern platforms abstract much of the complexity behind intuitive graphs and guided investigations. Over time, analysts develop a stronger adversarial mindset, learning to think in entities and paths rather than isolated alerts.
Useful metrics include reduction in false positives, time‑to‑detect and time‑to‑contain for identity and cloud‑native attacks, number of exploitable attack paths to crown‑jewel assets, and mean risk score across key entity classes. Platforms like ion can track these over time, allowing you to show tangible improvement in blast radius, detection quality, and operational workload.
By embracing contextual & entity‑centric threat detection, and operationalizing it through a graph‑driven, multi‑cloud platform like ion Cloud Security, organizations can move from reactive alert chasing to proactive, attacker‑aware defense that meets the realities of modern cloud and AI‑driven risk.