It is 2:47 AM on a Tuesday. Your on-call engineer gets paged – not by your SIEM, not by your cloud provider’s native alerts, but by a journalist asking for comment on a data exposure that has already been circulating on a Telegram channel for six hours. A public S3 bucket. A misconfigured IAM role. A developer who spun up a test environment three weeks ago and forgot to remove the public access block. Three unremarkable misconfigurations, none of which tripped a single alert in isolation. Together, they created an attack path to 40,000 customer records.
This is the cloud security problem that CNAPP was built to solve. Not the theoretical multi-stage attack that lives in conference keynote decks. The ordinary, preventable, compounding failure mode that plays out in thousands of cloud environments every month – including, statistically, ones that look a lot like yours.
Cloud-native application protection platform (CNAPP) is the architectural response to a specific failure: the inability of isolated security tools to see the connections between cloud misconfigurations, identity risks, workload vulnerabilities, and network exposure that attackers exploit every day. CNAPP consolidates the detection, prioritization, and response capabilities that most enterprises currently run as five or six separate tools – each producing its own alerts, each missing the context held by the others.
CNAPP (Cloud-Native Application Protection Platform) is a unified cloud security architecture that integrates cloud security posture management (CSPM), cloud workload protection (CWPP), identity security (CIEM), and shift-left development security into a single platform — replacing multiple disconnected tools with correlated, contextual protection across the full cloud application lifecycle.
This guide is for the CISO who is tired of getting breach post-mortems that describe problems their tooling technically detected – just not in a way anyone could act on. It is for the DevSecOps lead who has watched their pipeline security gates become checkbox theatre because nobody connected the CI/CD findings to the runtime environment. And it is for the CTO who needs to explain to their board why cloud security investment keeps going up while incident frequency does not go down.
In This Guide, You Will Learn:
- The precise definition of CNAPP and the architectural logic that makes it different from tool bundles
- How CNAPP compares to CSPM, CWPP, CASB, and CIEM – with a clear decision framework for each
- The 5-Layer CNAPP Architecture Model – a named framework for evaluating and implementing cloud-native security
- Real-world application across Indian BFSI, GCC, SaaS, and telecom archetypes
- Eight strategic recommendations for security leaders, plus a where-to-start triage for overwhelmed teams
- India-specific regulatory implications: CERT-In, DPDP Act, RBI, SEBI frameworks
The Cloud Security Stack Is Growing. The Threat Surface Is Growing Faster.
Most enterprise cloud security architectures were not designed; they accumulated. A CSPM tool added after the first compliance audit. A CWPP agent deployed after a container vulnerability scare. A separate identity governance platform after a privilege escalation incident. A CASB layer when the CISO’s peer network started talking about shadow IT. Each tool was a rational response to a real problem at the time it was purchased. Collectively, they created an architecture that nobody designed and nobody fully understands.
The IBM Cost of a Data Breach Report 2023 found that organizations with fully deployed security AI and automation identified and contained breaches 108 days faster than those without – a gap that directly translates to data volume exposed and regulatory consequence incurred. Yet the same research found that 82% of breaches involved cloud-stored data, and the mean time to identify a breach across the industry remained at 204 days. These two findings sit in direct tension: the tools exist, but the architecture to make them work together does not.
Did You Know?
The root problem is contextual blindness. A CSPM tool sees that an EC2 instance has a public IP address and an overly permissive security group. A CWPP tool sees that the same instance is running a container with an unpatched critical vulnerability. An identity governance platform sees that the IAM role attached to that instance has never been reviewed and grants S3 full access to production buckets. None of these tools know what the others know. So the CSPM raises a medium-severity misconfiguration alert. The CWPP raises a high-severity vulnerability alert. The identity tool raises a governance flag that sits in a backlog. And the actual attack path – public network access, exploitable vulnerability, excessive IAM permissions, sensitive data exposure – is never surfaced as the critical, unified risk it represents.
Do Give it a Read: Cloud Attack Path Analysis & Graph-Based Risk Modeling: The Missing Link in Cloud Security
India Context: The Compliance Pressure Point?
CERT-In’s April 2022 directive mandating 6-hour breach reporting windows fundamentally changed the operational calculus for Indian security teams. When CERT-In says you must report a breach within 6 hours, you need to know you have been breached within minutes – not days.
The DPDP Act 2023 has added a second layer: data processing organizations now face mandatory breach notification to the Data Protection Board, with penalties that the industry expects to be enforced with increasing frequency through 2025 and 2026. RBI’s revised IT Governance Master Direction places additional continuous monitoring obligations on BFSI entities that scheduled scan-based tools cannot satisfy.
Expert Insight
The fundamental failure of the point-solution model is not that the tools are bad – most of them are technically competent at what they do individually. The failure is architectural: security intelligence that does not flow between tools cannot protect an environment where threats flow across every layer simultaneously. An attacker exploiting a misconfigured cloud storage bucket does not care that your CSPM and your CWPP report to different dashboards. They simply move along the path of least resistance. Your job, as the defender, is to see that path before they take it – and that requires a unified view that siloed tools are structurally incapable of providing.
The consequence is not just operational inefficiency; it is a measurable security gap. The Verizon Data Breach Investigations Report 2023 found that 74% of breaches involved a human element: not necessarily because humans made mistakes, but because the volume and fragmentation of alerts made it impossible for humans to identify the signals that mattered. Security teams were not failing because they lacked talent. They were failing because their architecture was producing an unprocessable volume of decontextualized findings. CNAPP represents the architectural correction to that specific failure mode.
Read More: Implementing CSPM in Multi-Cloud & Hybrid Environments: The 2026 Survival Guide
The Assumption That Is Leaving Your Most Dangerous Exposure Untouched
Most cloud security programs are organized around the assumption that more coverage means better security. More tools, more controls, more checklists. This assumption is so deeply embedded in enterprise security procurement that most security leaders do not examine it; they simply execute it.
The coverage assumption conflates detection surface with security effectiveness. The attacker who crafts a path that crosses all five categories – misconfiguration, vulnerable workload, excessive permissions, exposed network, sensitive data; is invisible to each individual tool.
Most security organizations believe that comprehensive tooling equals comprehensive protection. The evidence suggests the opposite: tool sprawl is one of the leading operational contributors to security failures in cloud environments, not because the tools are inadequate, but because the architecture they create is.
| Most Common Approach | The Better Approach for Future |
|---|---|
| Waiting for SIEM alerts to discover cloud misconfigurations – by which time a change may have been exploitable for hours | Event-driven detection that evaluates misconfigurations the moment a configuration change occurs, before the window of exposure begins |
| Running CSPM scans on a 24-hour schedule because that is what the tool supports by default | Continuous posture assessment triggered by infrastructure events in real time – every deployment, every permission change, every network modification |
| Triaging vulnerability scanner output by CVSS score, sending 2,400 findings to developers who cannot distinguish critical from irrelevant | Context-aware vulnerability prioritization that surfaces only the vulnerabilities on publicly reachable, over-permissioned, running workloads – typically 5% of the raw finding volume |
| Treating identity governance as a quarterly review exercise separate from cloud security operations | Continuous identity posture monitoring that flags over-privileged, unused, and MFA-absent identities in the same risk view as network and workload findings |
| Reporting to the board on the number of findings closed – a metric that rewards alert volume, not risk reduction | Reporting on attack path reduction: how many exploitable chains from public access to sensitive data were eliminated this quarter |
“The security team that closes the most alerts is not winning. The security team that eliminates the most attack paths is winning – and those are fundamentally different objectives that require fundamentally different architecture.”
The CNAPP category was created precisely to address this architectural failure. A purpose-built CNAPP shares context across every security domain: posture, identity, workload, network, compliance. A finding in any one domain enriches the understanding of every other.
A Relatable Read for You: How Indian Enterprises Are Finally Solving the Multi-Cloud Security Complexity Gap
What Is CNAPP? Definition, Architecture, and the 5-Layer Cloud-Native Security Model
The Working Definition
A Cloud-Native Application Protection Platform (CNAPP) is a unified security architecture that integrates cloud security posture management (CSPM), cloud workload protection (CWPP), cloud infrastructure entitlement management (CIEM), Kubernetes security posture management (KSPM), and vulnerability management into a single platform with a shared data model and contextual correlation engine. CNAPP is not a feature set; it is an architectural principle: that cloud security intelligence must be unified to be effective.
Gartner introduced the CNAPP category in 2021 to describe what the market was converging toward: the recognition that cloud-native environments require protection across the full lifecycle – from development pipelines through runtime; and that this protection cannot be delivered by tools that do not share context with one another.
CNAPP vs CSPM vs CWPP vs CASB: The Definitive Comparison
Table: CNAPP vs CSPM vs CWPP vs CASB — Feature-by-Feature Comparison (Updated 2026)
| Capability | CNAPP | CSPM | CWPP | CASB |
|---|---|---|---|---|
| Cloud Posture Management | ✓ Native | ✓ Primary | — Partial | ✗ No |
| Workload & Container Protection | ✓ Native | ✗ No | ✓ Primary | ✗ No |
| Runtime Threat Detection | ✓ Native | ✗ No | — Partial | ✗ No |
| Shift-Left / IaC Scanning | ✓ Native | — Partial | — Partial | ✗ No |
| Identity Risk (CIEM) | ✓ Native | — Limited | ✗ No | — Partial |
| Attack Path Correlation | ✓ Native | ✗ No | ✗ No | ✗ No |
| SaaS & Shadow IT Visibility | — Partial | ✗ No | ✗ No | ✓ Primary |
| India Regulatory Mapping (CERT-In, RBI) | — Vendor-dependent | ✗ Rare | ✗ Rare | ✗ Rare |
| Replaces Multiple Point Tools | ✓ Yes (4–6 tools) | ✗ No | ✗ No | ✗ No |
✓ = Full capability | — = Partial / limited | ✗ = Not covered. Source: Cy5.io analysis, Gartner Cloud Security market research 2024–2025.
The 5-Layer CNAPP Architecture Model
Evaluating any CNAPP platform; or designing an implementation roadmap – becomes significantly clearer when you apply a structured architectural lens. The 5-Layer CNAPP Architecture Model provides that lens, breaking unified cloud-native security into five interdependent layers that must all function correctly for the platform to deliver its intended outcome.
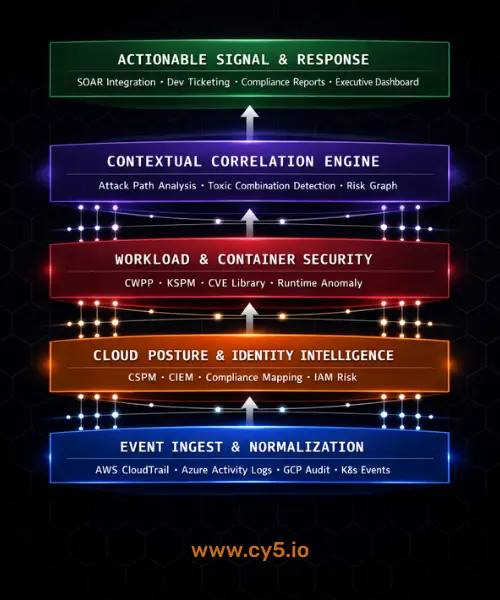
Layer 1: Event Ingest and Normalization
The foundation of any effective CNAPP is the ability to ingest security-relevant events from every layer of the cloud stack – in real time, not on a schedule. This means API-level integration with AWS CloudTrail, Azure Activity Logs, GCP Audit Logs, Kubernetes audit logs, container runtime events, and application telemetry. Events must be normalized into a common schema that allows correlation across cloud providers and service types.
What good looks like: A new S3 bucket with public access enabled triggers an evaluation within seconds of creation; not hours. The event data is enriched with asset context (owner, environment, data classification, existing relationships to other resources) before it reaches the correlation layer.
Common Mistakes
Relying on scheduled API polling rather than event-driven ingest. This creates detection blind spots between scan intervals – exactly the window attackers use to establish initial access, exfiltrate data, and clean up evidence. In India’s CERT-In 6-hour reporting context, a 24-hour scan schedule is operationally incompatible with compliance requirements.
India implementation note: Indian enterprises running hybrid environments where on-premises infrastructure coexists with multi-cloud deployments need an ingest layer that handles both cloud-native event streams and syslog/SIEM forwarding from legacy systems. This hybrid ingest capability is often the first gap discovered when Indian organizations evaluate CNAPP platforms built primarily for pure-cloud environments.
Layer 2: Cloud Posture and Identity Intelligence
CSPM and CIEM functions form the second layer; the continuous assessment of what your cloud environment looks like from an attacker’s perspective. This encompasses misconfiguration detection across 100+ resource types, compliance posture mapping to frameworks like CIS Benchmarks, ISO 27001, SOC 2, and India-specific regulatory controls, and continuous entitlement analysis that identifies which identities hold which permissions and whether those permissions are actively used, necessary, or dangerous.
Do Give it a Read: Cloud Misconfiguration Detection: Complete Guide for 2026 (AWS, Azure, GCP & Best Practices)
What good looks like: Every IAM role in every cloud account is continuously evaluated against actual usage patterns. Roles that hold permissions they have never exercised, that have no MFA requirement, that are attached to compute instances with public network access – these surface automatically as prioritized identity risks, not as governance backlog items.
Common Mistake
Treating identity governance and cloud posture as separate workstreams managed by different teams. This organizational silo directly maps to the technical blind spot that attackers exploit: the intersection of misconfigured infrastructure and over-privileged identities is the most common path to breach, and it is invisible when the tools do not share data.
Layer 3: Workload and Container Security
The third layer addresses runtime security for virtual machines, containers, serverless functions, and Kubernetes clusters. This includes agentless vulnerability scanning that identifies CVEs in running workloads and container images, runtime anomaly detection that flags unusual process execution or network behavior, and Kubernetes Security Posture Management (KSPM) that evaluates cluster configurations against security best practices.
What good looks like: Vulnerability findings are not presented as a raw CVE list sorted by CVSS score. They are contextualized: a critical CVE on an internet-facing container that has never been patched, is running with elevated privileges, and exists in a cluster with permissive network policies is a fundamentally different risk than the same CVE on an internal development workload with no network exposure. The platform surfaces only the former as requiring immediate action.
Common Mistake
Deploying agent-based CWPP solutions that require significant DevOps effort to maintain across dynamic containerized environments. In organizations where Kubernetes clusters scale horizontally and containers are ephemeral, agent deployment and lifecycle management becomes a full-time operational burden that consumes more security team capacity than the protection it provides.
India implementation note: Indian fintech and GCC organizations running containerized microservices on managed Kubernetes services (EKS, AKS, GKE) face a specific challenge: the container image supply chain. Images often originate from open-source base images with known vulnerabilities, are modified by development teams who are not security specialists, and are deployed at velocity that outpaces manual security review. Agentless KSPM with integrated image scanning addresses this without requiring development team process changes.
Must Read: Vulnerability Management in the Age of AI: Empowering Cloud Security
Layer 4: Contextual Correlation Engine
This is the layer that separates a genuine CNAPP from a tool bundle with a common dashboard. The contextual correlation engine ingests findings from all other layers and identifies the relationships between them – the specific combinations of misconfiguration, identity risk, workload vulnerability, and network exposure that together constitute an exploitable attack path. Rather than generating thousands of individual findings, it surfaces the chains of risk that represent real-world exposure.
What good looks like: “Public network access (0.0.0.0/0) → overly permissive compute → unpatched critical vulnerability → IAM role with full S3 access” is surfaced as a single, prioritized attack path with a specific recommended remediation sequence; not as four separate findings in four separate tool queues.
Cy5’s ion Cloud Security platform operationalizes this layer through its contextual correlation engine, which maps relationships between cloud configurations, identities, network paths, and workload vulnerabilities to identify what its architecture calls “toxic combinations” – specific chains of individually manageable risks that together create genuine attack vectors. Rather than thousands of isolated alerts, the platform surfaces the specific risk chains that, if exploited in sequence, could lead to data breach or service disruption.
Common Mistake
Confusing data aggregation with correlation. Many platforms marketed as CNAPP collect findings from multiple tools into a common database but do not actually analyze the relationships between findings. The result is a unified alert queue, not a unified intelligence layer. The test is simple: can the platform show you, graphically, the specific path from initial exposure to a crown-jewel asset? If not, it is aggregating, not correlating.
Layer 5: Actionable Signal and Response
The output layer of a CNAPP must convert correlated intelligence into actions; not recommendations. This means integration with SOAR platforms for automated response playbooks, ticketing system integration that creates actionable developer tickets with specific remediation guidance, compliance reporting that maps posture findings to regulatory frameworks, and executive dashboards that communicate risk in business terms rather than security jargon.
What good looks like: When a critical attack path is identified, the platform automatically creates a ticket in Jira or ServiceNow with the specific misconfiguration, the affected resource, the recommended fix, the compliance implications, and the severity context. A developer can remediate it without ever opening the security platform. Security teams measure their success by the reduction in exploitable attack paths, not the number of findings closed
Common Mistake
Designing the response layer primarily for security analysts rather than for the developers who own the infrastructure. Attack paths are created by infrastructure changes made in development. The most effective CNAPP implementations put actionable, contextual security guidance directly into the development workflow; in the IDE, in the CI/CD pipeline, and in the ticketing systems developers already use.
CNAPP in the Indian Enterprise: Four Scenarios That Changed the Calculation
🇮🇳 Why CNAPP India Adoption Is Accelerating
CNAPP adoption in India is being driven by a convergence of regulatory pressure, rapid multi-cloud expansion, and a shortage of cloud security specialists. Indian enterprises — particularly in BFSI, IT/ITeS, and healthcare — face a unique compliance environment: CERT-In 2022 mandates 6-hour breach reporting, RBI IT Governance circulars require continuous cloud risk monitoring, and the DPDP Act introduces data localisation obligations that point tools simply cannot track across hybrid environments.
For CNAPP for BFSI India specifically, the stakes are highest: NBFCs, payment processors, and digital lenders operate on cloud infrastructure that must simultaneously satisfy RBI audit requirements, PCI-DSS controls, and real-time fraud detection — a combination that only a unified CNAPP architecture can address without engineering paralysis.
Scenario 1: The Series C Fintech That Discovered Its API Was Doing Double Duty
Context: A Bengaluru-based Series C SaaS company running its core platform on AWS had been growing fast; 40 engineers, three cloud accounts, microservices architecture, no dedicated cloud security hire. Their security posture was managed through periodic manual reviews and a basic CSPM subscription.
The specific risk: An internal API endpoint, originally deployed for a deprecated feature, had been retained because one legacy service still called it. The endpoint was technically still accessible from 0.0.0.0/0; the original developer had added the public access to test it and intended to remove it after deployment. The same service account used to serve this endpoint had, at some point, been granted broad read access to the production data lake as part of a different feature’s development. Neither the open network access nor the excessive permission had tripped any alert individually. Together, they represented a path from the public internet to 2.3 million user records.
What a CNAPP deployment would have surfaced: The contextual correlation layer would have identified the specific chain: public network access → deprecated but live endpoint → service account with production data lake access → unencrypted data store. This combination would have been surfaced as a critical attack path within seconds of the service account’s permission being expanded; not discovered in a quarterly security review. Remediation time under this model: under two hours. Actual discovery timeline: 14 weeks after the exposure was created, during a compliance audit initiated for a Series D funding due diligence.
The outcome difference: The company disclosed the exposure proactively as part of the audit process. Under CERT-In’s 6-hour reporting mandate, had this been discovered following an actual breach rather than an audit, the reporting timeline alone would have generated regulatory scrutiny. The CISO responsible for the gap estimated the cost of the compliance remediation program that followed at approximately ₹80 lakhs; against a CNAPP platform cost of roughly ₹15 lakhs annually.
Scenario 2: A Tier-1 NBFC Navigating the RBI IT Governance Circular
Context: A Mumbai-based Non-Banking Financial Company with assets under management exceeding ₹25,000 crores had been operating its core lending platform on Azure for three years. Following RBI’s revised Master Direction on IT Governance, it initiated a cloud security assessment as part of its compliance program. The assessment was performed by a consulting firm using a combination of Azure Security Center findings and manual review.
The specific risk: The assessment identified 847 open findings across cloud configurations. 15 were rated critical, 203 high, the remainder medium and low. The security team, four people covering all of IT security, had no realistic capacity to triage 847 findings while managing day-to-day operations. The consulting firm prioritized by CVSS score. The actual highest-risk issue; a service account with Azure Active Directory write permissions that was being used by a publicly accessible Azure Function handling loan disbursement API calls; was rated high, not critical, because the CVSS-based methodology did not account for the business criticality of the data it could access or the accessibility of the entry point.
What effective CNAPP would have changed: A contextual correlation engine evaluating the same environment would have immediately identified the toxic combination: public-facing function + excessive identity permissions + access to core financial transaction data + no network restriction = critical attack path to RBI-regulated financial data. This specific finding would have appeared at the top of a short, contextual risk list rather than 143rd in a ranked CVSS list. The team’s four analysts would have spent their first day on the finding that actually mattered.
The outcome difference: The NBFC remediated the actual critical risk in week one of a planned 12-week program. The team’s morale, which had been deteriorating under the weight of an unprocessable findings backlog, measurably improved once the alert volume was contextualized. The compliance report submitted to RBI documented the remediation timeline and the platform architecture, which the RBI inspection team reviewed favorably as evidence of continuous monitoring capability; a specific requirement of the Master Direction.
Must Read: Cloud Attack Path Analysis & Graph-Based Risk Modeling: The Missing Link in Cloud Security
Eight Strategic Recommendations for Security Leaders Evaluating CNAPP
1. Audit Your Current Tool Stack Against the 5-Layer Model
Before evaluating any platform, map your existing tools to the five layers of the CNAPP architecture model. Most organizations discover that they have partial coverage in each layer but no correlation between them. This exercise typically reveals three things: redundant tools covering the same layer (producing duplicate alerts), missing layers with no coverage at all, and zero architecture connecting the layers they do have. This map becomes your CNAPP business case.
Signal that you have done this correctly: You can draw a diagram showing how a finding generated in Layer 1 flows to enrich a finding in Layers 2, 3, and 4; and if you cannot draw it, your architecture cannot execute it.
2. Replace Scheduled Scans with Event-Driven Posture Assessment
If your primary cloud security tool operates on a scheduled scan model; even a 4-hour or 1-hour schedule; you have a detection blind spot that covers exactly the window attackers exploit. Cloud environments change faster than any scheduled scan can track: deployments, permission changes, network modifications, and data access patterns occur continuously. Transitioning to event-driven architecture, where posture is evaluated the moment any infrastructure change occurs, eliminates this blind spot entirely. This is a non-negotiable requirement for compliance with CERT-In’s 6-hour reporting mandate.
Signal that you have done this correctly: Your team can identify the specific moment any misconfiguration was introduced, not just that it exists now. Forensic precision in posture management is only possible with event-driven architecture.
3. Unify Identity and Infrastructure Security Under a Single Risk View
The most exploitable attack paths in cloud environments consistently combine infrastructure misconfiguration with identity risk. Public network access plus overly permissive IAM roles is not two medium-severity findings; it is a critical attack path. Your architecture must be capable of seeing this combination, which means your cloud posture and identity governance functions must share data. If your CSPM and your IAM governance platform do not share a data model and cannot correlate findings, you have a structural blind spot covering the most common breach pattern in cloud environments.
Signal that you have done this correctly: You can run a query that shows you every internet-accessible resource that has an IAM principal attached with unused elevated permissions. If this query takes more than 30 seconds and requires manual export and cross-referencing, your architecture is not unified.
4. Implement Shift-Left Security in Your Development Pipeline; But Connect It to Runtime
Shift-left security: scanning infrastructure-as-code, container images, and application dependencies before deployment; is now standard advice, and it is good advice. But it creates a false sense of security if it is not connected to the runtime environment.
Code that passes pre-deployment security gates can be deployed into a runtime context that creates new risks: a container that was clean at build time may be running in a cluster with permissive network policies, alongside an over-privileged service account, on a node with an unpatched kernel vulnerability. The shift-left and the runtime view must share context to catch this.
Signal that you have done this correctly: Your CI/CD pipeline findings and your runtime posture findings reference the same resource identifiers and appear in the same risk view. A developer can see, in their pipeline, the runtime context of the environment they are deploying into.
Read More: How to Implement Secure Design Principles in Cloud Computing: The 2025 Practitioner’s Playbook
5. Prioritize Attack Paths, Not Finding Counts; And Change How You Report Upward
The metric most commonly reported to boards and leadership teams; number of security findings, number of findings remediated, percentage of findings closed; is the wrong metric. It rewards alert volume and closure velocity, neither of which correlates with actual security outcome. The metric that correlates with breach risk reduction is the number of exploitable attack paths from the public internet to sensitive data. This metric is harder to measure with traditional tools and requires CNAPP-level contextual correlation to produce reliably. But it is the metric your board is actually asking about when they ask whether you are secure.
Signal that you have done this correctly: Your last board security report included the phrase ‘exploitable attack paths’ and showed a trend line. If it showed finding counts instead, you are reporting operational activity, not security posture.
6. Address the India Regulatory Compliance Gap Explicitly in Your Platform Evaluation
Many CNAPP platforms have been designed primarily for US and European regulatory frameworks; SOC 2, GDPR, FedRAMP. Indian enterprises evaluating CNAPP must specifically verify: prebuilt compliance packs for CERT-In guidelines, RBI Master Direction mapping, DPDP Act data classification controls, and SEBI cybersecurity framework requirements. Platforms without native India regulatory support force security teams to manually maintain compliance mapping; work that eliminates much of the operational efficiency gain that CNAPP is supposed to provide. This is an especially critical evaluation criterion for BFSI organizations.
Urgency factor: The Data Protection Board established under the DPDP Act 2023 is expected to issue its first enforcement actions in 2025-2026. Organizations that cannot demonstrate continuous data protection posture; including cloud security controls over data-containing infrastructure, will face both regulatory exposure and reputational risk.
7. Evaluate Total Cost of Ownership, Not License Cost
The most common mistake in CNAPP procurement is comparing license costs across platforms without accounting for the operational cost of the alternatives. A platform that costs 40% more than its competitor but eliminates three separate tool subscriptions, reduces analyst time on alert triage by 80%, and cuts mean time to detect from 48 hours to under 30 minutes delivers dramatically better TCO, even before accounting for the breach cost it prevents. Indian security leaders face particular pressure from CFOs and procurement committees to minimize license spend. The business case for CNAPP must be built on TCO and breach cost avoidance, not on subscription line comparison.
Organizations that have deployed unified CNAPP platforms report documented outcomes that illustrate the TCO case: Cy5’s ion platform customers across Indian telecom and fintech have reported 97% reduction in mean time to detect, 85-96% reduction in alert noise, and the operational equivalent of 3 person-months per year saved in security operations overhead, all of which represent TCO benefits that a license cost comparison cannot capture.
8. Build Your CNAPP Implementation Roadmap in 90-Day Horizons, Not Big-Bang Deployments
The most common implementation failure for CNAPP is the attempt to deploy everything simultaneously. Full-stack CNAPP implementation across a complex cloud environment involves cloud account onboarding, alert tuning, compliance framework mapping, SIEM integration, developer workflow integration, and organizational change management. Attempting all of this in parallel guarantees failure. The organizations that achieve full CNAPP value within 12 months invariably begin with a single, high-priority use case; typically cloud posture and identity risk for production environments, demonstrate measurable outcome improvement within 90 days, and expand from there.
Signal that you have done this correctly: At the end of your first 90 days, you can show the specific attack paths that were identified and remediated that would not have been visible with your previous architecture. That demonstration is your expansion business case.
Where to Start? A 3-Step Triage for Overwhelmed Team
Step 1 (Week 1): Run a blind spot assessment. Map your current tools to the 5-Layer CNAPP Architecture Model. Identify which layers have no coverage and which have coverage but no correlation to other layers. This is your prioritized gap list.
Step 2 (Weeks 2-4): Instrument your highest-risk environment first. Onboard your production cloud accounts to a CNAPP platform with event-driven architecture. Do not start with development or staging; start where a breach would matter most. Generate your first correlated risk view within 48 hours of onboarding.
Step 3 (Month 2-3): Replace your top three alert sources with correlated intelligence. Identify the three tools generating the most noise with the least actionable output. Remove them from the alert workflow as the CNAPP correlation engine replaces their signal with contextualized, high-fidelity findings. Measure the reduction in alert volume and analyst triage time; this is your TCO proof point.
What the Research Says: Third-Party Validation of CNAPP as the Cloud Security Architecture
The shift toward unified cloud-native security is not a vendor narrative, it is a documented industry movement supported by independent research, enterprise adoption data, and measurable security outcomes.
Gartner’s 2023 Cloud Security Hype Cycle identified CNAPP as one of the highest-priority investments for enterprise security leaders, noting that organizations deploying unified CNAPP architectures demonstrated measurably better security outcomes than those maintaining equivalent capability through point-solution stacks. Gartner’s research specifically cited contextual correlation; the ability to identify relationships between findings across security domains, as the primary differentiator between CNAPP platforms that deliver outcome improvement and those that deliver only operational consolidation.
Expert Insight: The MITRE Att&ck Lens
MITRE ATT&CK for Cloud (available at attack.mitre.org) documents 13 primary tactics and 79 techniques used by threat actors against cloud environments. Analyzing these techniques reveals a critical pattern: 67% of documented cloud attack sequences involve multiple tactics executed in sequence; initial access followed by discovery, then privilege escalation, then exfiltration. Each individual tactic may be detectable by a single-domain tool. The attack sequence – the chain from initial access to data exfiltration – is only detectable by a platform that correlates across tactics. This is precisely the correlation gap that CNAPP is architected to close, and it is why point-solution stacks that individually detect each technique still fail to prevent multi-stage breaches.
For Indian enterprises specifically, the Data Security Council of India (DSCI) has published cloud security guidance that emphasizes continuous monitoring, contextual risk assessment, and integrated compliance management, all core CNAPP capabilities. DSCI’s engagement with CERT-In on cloud security standards suggests that India-specific cloud security regulation is moving in a direction that favors automated, continuous, unified security approaches over periodic manual assessments.
Cy5 has operated in the Indian cloud security market for over four years, maintaining 100% customer retention across its deployment base. Its ion platform serves organizations across fintech, telecom, ed-tech, and enterprise IT in India, the UK, Germany, Indonesia, Uganda, and the UAE; with documented outcomes including 97% MTTD reduction in telecom deployments and 85-96% alert noise reduction in fintech environments. Cy5’s open-source contributions (dataShark and Blitz) and active participation in the GRMI and EC-Council communities signal the kind of genuine practitioner-community engagement that distinguishes security companies with real operational depth from those with primarily marketing presence.
Forrester Research identifies CNAPP as the primary consolidation architecture for cloud security, projecting that enterprises replacing 5+ point tools with a unified CNAPP platform reduce security operations overhead by 35–50% over a 3-year horizon. Source: Forrester, Cloud Security Market Forecast, 2024.
CNAPP compliance automation eliminates the manual evidence-gathering burden that consumes 60–80% of audit preparation time in Indian enterprises. By continuously mapping cloud configurations to CERT-In, RBI, and SEBI CSCRF controls, CNAPP reduces audit preparation from weeks to hours.
The CNAPP lifecycle covers four phases:
(1) Build:
IaC scanning and developer security gates;
(2) Deploy: container image
scanning and registry enforcement;
(3) Run: runtime threat detection
and anomaly correlation;
(4) Govern: continuous compliance automation
and risk reporting. Unlike CSPM or CWPP alone, CNAPP covers all four.
The CISO Who Saw This Coming
The next cloud breach at a major Indian enterprise will not be caused by a sophisticated zero-day attack. It will be caused by an ordinary misconfiguration, an over-permissioned identity, and an unpatched workload – three findings that each exist in some security tool’s output queue today, unconnected to each other, untriaged in a backlog of thousands. The attacker will simply follow the path that those three unconnected findings create. Your tools will detect each element. None of them will see the path.
This is not pessimism, it is the statistical reality of cloud security in 2025 and 2026. It is also, importantly, a solvable problem. The CNAPP architecture exists precisely because the security industry has diagnosed this failure mode clearly and built a structural response to it. The question is not whether CNAPP is the right architectural direction; the research, the regulatory trajectory, and the documented outcomes make that clear. The question is whether your organization gets there before or after an incident that makes the decision for you.
The CISOs who position their organizations well in this environment share a specific characteristic: they stopped measuring security effectiveness by tool coverage and started measuring it by attack path elimination. They are the ones who can walk into a board meeting and say, not ‘we have tools covering 14 control domains,’ but ‘we have reduced the number of exploitable paths from the public internet to our sensitive data from 340 to 7 this quarter, and here is how.’ That is the conversation that builds lasting board confidence. And it is only possible with an architecture that can see paths, not just findings.
CERT-In’s reporting requirements, the DPDP Act‘s data protection obligations, RBI’s continuous monitoring expectations, and the SEBI cybersecurity framework are not going to become less demanding. The regulatory trajectory in India is moving toward more stringent, more real-time, more evidence-based security requirements – a direction that is directly aligned with what CNAPP is built to satisfy. Organizations that build CNAPP architecture now are building for the regulatory environment of 2026 and 2027, not just for today.
Ready to See Your Cloud Attack Surface as an Attacker Does?
If you are navigating any of what this guide describes; fragmented tooling, alert overload, an audit cycle that feels like it is outpacing your team’s capacity, or a board conversation that you are not sure how to have, we would genuinely like to understand your situation. Not to pitch you.
To understand the specific shape of the problem in your environment.→ Request a Cloud Security Architecture Review with Cy5’s team – cy5.io/contact
No commitment. No deck. The first conversation is a genuine security discussion.
Questions Security Leaders Ask About CNAPP
CNAPP stands for Cloud-Native Application Protection Platform. It is a unified security architecture that integrates multiple cloud security disciplines – cloud security posture management (CSPM), cloud workload protection (CWPP), cloud infrastructure entitlement management (CIEM), Kubernetes security posture management (KSPM), and vulnerability management – into a single platform with a shared data model. The defining capability of a genuine CNAPP is contextual correlation: the ability to identify relationships between findings across security domains and surface the specific combinations of risk that together constitute exploitable attack paths.
CNAPP stands for Cloud-Native Application Protection Platform. The term was introduced by Gartner in its 2021 Innovation Insight research to describe the convergence of cloud security tools into a unified platform architecture. The “application protection” in the name reflects the platform’s scope across the full application lifecycle, from development pipelines and infrastructure-as-code through runtime workload security and posture management.
CSPM (Cloud Security Posture Management) is one component of CNAPP; specifically the component responsible for detecting and remediating cloud infrastructure misconfigurations. CNAPP encompasses CSPM but adds workload security (CWPP), identity entitlement management (CIEM), Kubernetes security (KSPM), and critically, a contextual correlation layer that CSPM tools lack. The difference in practice: CSPM tells you that an EC2 instance has a public IP and an overly permissive security group. CNAPP tells you that this instance also has an unpatched critical vulnerability, is running with a service account that has full S3 access, and together these four factors create a critical attack path to your production data; a finding that CSPM alone cannot surface.
CNAPP incorporates CWPP capabilities rather than replacing CWPP as a concept. A fully implemented CNAPP platform includes workload and container security (the domain CWPP covers), but integrates it with cloud posture, identity, and compliance functions that standalone CWPP tools lack. For organizations currently running a dedicated CWPP solution alongside a CSPM tool, a CNAPP platform typically consolidates both under a unified data model – reducing operational overhead and enabling the cross-domain correlation that neither tool can provide independently. The question to ask any CNAPP vendor is whether their workload protection is native to the platform or an acquired product grafted onto a different architecture.
A complete CNAPP platform includes five core components:
(1) CSPM – continuous cloud infrastructure misconfiguration detection and compliance mapping;
(2) CWPP – workload and container security covering vulnerability scanning, runtime protection, and image security;
(3) CIEM — cloud identity entitlement management for identifying over-privileged, unused, and risky IAM configurations;
(4) KSPM — Kubernetes-specific security posture monitoring for container orchestration environments;
(5) Contextual Correlation Engine — the architectural component that connects findings across all domains to identify multi-step attack paths.
Some CNAPP platforms also include SIEM integration, SOAR-ready alerting, and a security data lake for analytics and threat hunting.
CNAPP is particularly critical for multi-cloud environments precisely because each cloud provider (AWS, Azure, GCP) has its own IAM model, logging format, network primitives, and compliance footprint. Without a unified CNAPP layer, security teams managing multi-cloud environments must maintain separate tools for each provider, creating visibility gaps at the intersections – the exact locations that sophisticated attackers exploit.
A CNAPP platform with native multi-cloud support normalizes findings across providers into a single risk view, enabling detection of attack paths that span cloud boundaries. For Indian enterprises managing workloads across multiple cloud providers (increasingly common in BFSI and GCC contexts), this cross-cloud correlation capability is not optional.
Enterprises are moving to CNAPP for three primary reasons. First, alert overload: the average enterprise security team receives thousands of daily security findings across cloud tools that it cannot practically triage, and CNAPP’s contextual correlation reduces this to a manageable number of high-fidelity, prioritized risk signals. Second, compliance pressure: regulators are increasingly requiring continuous cloud monitoring with evidence of real-time detection and response capability – a standard that scheduled-scan CSPM tools cannot meet. Third, economics: maintaining five to eight separate cloud security tools with overlapping coverage costs more than a unified CNAPP platform, particularly when total cost of ownership includes analyst time spent on tool management rather than security work.
CNAPP enables the shift-left security model that DevSecOps requires by integrating security evaluation directly into development pipelines – scanning infrastructure-as-code, container images, and application dependencies before deployment. Critically, CNAPP connects pre-deployment findings to runtime context: a developer can see not just that their code has a vulnerability, but that the environment they are deploying into has specific exposure characteristics that make that vulnerability exploitable. This runtime context is what separates genuinely effective DevSecOps integration from checkbox security scanning that developers learn to ignore.
CERT-In’s 6-hour breach reporting mandate requires Indian organizations to detect incidents within a window that traditional scheduled-scan CSPM tools cannot support. CNAPP platforms with event-driven architecture detect misconfigurations and threats the moment they occur – not on the next scheduled scan — which is the operational prerequisite for 6-hour reporting compliance.
Additionally, CNAPP platforms with prebuilt CERT-In compliance packs automate the mapping of security findings to CERT-In advisory requirements, reducing the manual effort required to demonstrate compliance during CERT-In inspections. Organizations subject to both CERT-In requirements and RBI or SEBI frameworks benefit from CNAPP’s ability to map a single finding to multiple regulatory frameworks simultaneously.
The best CNAPP platform for Indian enterprises combines four capabilities that global platforms often lack: native India regulatory compliance packs (CERT-In, DPDP Act, RBI, SEBI framework mapping), multi-cloud support for the AWS, Azure, and GCP environments most prevalent in Indian enterprise deployments, hybrid ingest capability for organizations with on-premises infrastructure that cannot be immediately migrated, and a track record of deployment in the Indian security environment.
Cy5’s ion Cloud Security platform was built in India for the Indian enterprise context and has documented deployments across Indian BFSI, telecom, and GCC organizations; with compliance mapping for India-specific regulatory requirements that global CNAPP platforms have been slower to incorporate.
CNAPP addresses identity risk through its CIEM component, which continuously analyzes which identities (users, service accounts, IAM roles) hold which permissions in cloud environments, compares granted permissions to actually-used permissions to identify over-privilege, flags identities with access keys but no MFA, and identifies dormant identities that retain permissions despite no recent activity.
The critical CNAPP differentiator is that identity findings are not evaluated in isolation – they are correlated with infrastructure posture findings. A service account with excessive permissions becomes a critical risk when correlated with the finding that the compute instance it is attached to has public network access and an unpatched vulnerability.
CNAPP is operationally valuable at any scale where cloud security is a real concern – which increasingly means Series A and Series B startups as well as large enterprises. For smaller organizations, the primary CNAPP benefit is different from large enterprises: it is not alert consolidation (a startup may not have an alert volume problem yet), but rather the prevention of the early architectural mistakes that create expensive remediation problems later. A startup that deploys a CNAPP platform during its initial cloud environment setup avoids accumulating the misconfiguration and identity debt that becomes very costly to remediate at scale. CNAPP also reduces the security team headcount required to manage cloud security effectively; a critical advantage for small security teams.
CNAPP reduces alert noise through contextual correlation: instead of generating individual alerts for every misconfiguration, vulnerability, and identity risk detected across the cloud environment, the correlation engine evaluates whether findings are related and surfaces only the combinations that represent genuine, exploitable risk. A simple example: 500 medium-severity misconfigurations across a cloud environment may contain three critical attack paths when correlated with identity and network context. A traditional CSPM tool would generate 500 alerts. A CNAPP correlation engine would generate three actionable attack path findings. Documented outcomes from Indian enterprise CNAPP deployments report 85-96% reduction in alert volume without a corresponding reduction in actual threat detection.
CNAPP and Zero Trust are complementary architectural principles, not competing ones. Zero Trust establishes the principle that no identity, device, or network location should be inherently trusted; all access should be verified continuously. CNAPP provides the visibility and intelligence layer that makes Zero Trust operationally achievable in cloud environments: CIEM components surface the identity risk landscape that Zero Trust access policies must address, CSPM detects the network misconfigurations that undermine Zero Trust network segmentation, and CWPP monitors runtime workloads for behavior that violates Zero Trust principles. CNAPP without Zero Trust lacks an enforcement model; Zero Trust without CNAPP visibility lacks the intelligence to know which risks to enforce against.
Initial CNAPP deployment; onboarding production cloud accounts and generating a first correlated risk view – can be achieved within 24-48 hours for organizations with well-organized cloud account structures. Full implementation across multi-cloud, hybrid, and Kubernetes environments, including compliance framework mapping, developer workflow integration, and SIEM/SOAR connectivity, typically requires 60-90 days for a focused team. The critical success factor is sequencing: start with production environments, validate the correlated risk output, demonstrate value to stakeholders, then expand to non-production accounts and additional integration points. Organizations that attempt simultaneous full-stack deployment consistently take longer and achieve lower initial adoption than those that follow a phased approach.
The Indian CNAPP market is at an inflection point driven by three converging forces: regulatory pressure (CERT-In, DPDP Act, RBI, SEBI frameworks all pushing toward continuous, automated cloud security); cloud adoption acceleration (Indian enterprises and GCCs adding cloud workloads faster than security teams can manually manage); and the growing recognition that point-solution architectures cannot scale to meet the threat environment Indian organizations face. NASSCOM’s 2023 cybersecurity report identified cloud security as the highest-priority investment area for Indian enterprises, with CNAPP specifically named as the emerging dominant architecture category. The India-specific CNAPP opportunity is amplified by the fact that most global CNAPP vendors have not fully incorporated India regulatory requirements; creating an opening for platforms built with the Indian context as a first-class design consideration.
Key Takeaways
- CNAPP is a unified security architecture; not a feature aggregation – defined by a contextual correlation engine that identifies exploitable attack paths across cloud posture, identity, workload, and network domains simultaneously.
- The point-solution model fails not because individual tools are inadequate, but because security intelligence that does not flow between tools cannot protect environments where threats flow across every layer.
- The 5-Layer CNAPP Architecture Model (Event Ingest → Posture & Identity → Workload Security → Contextual Correlation → Actionable Signal) provides a structured framework for evaluating platforms and designing implementation roadmaps.
- India-specific regulatory requirements; CERT-In 6-hour reporting, DPDP Act data protection obligations, RBI continuous monitoring mandates; are operationally incompatible with scheduled-scan CSPM tools and require event-driven CNAPP architecture.
- CNAPP’s primary security metric is not finding count but attack path elimination: the reduction in exploitable paths from the public internet to sensitive data assets.
- Effective CNAPP implementation follows a 90-day phased approach: production account onboarding first, validated correlated risk output second, expand and integrate third.
- Total cost of ownership; including analyst time, tool overlap, and breach cost avoidance, consistently favors CNAPP consolidation over equivalent point-solution stacks, even when license costs appear higher.
About the Author

Vikram brings 20 years of hands-on security experience spanning offensive security, cloud security engineering, and fraud management. As CISO at MakeMyTrip Group (2012–2021), he won the DSCI Excellence Award three times. Before that, he worked with IBM Security (2008–2012). He founded Cy5.io to build the cloud security platform he wished had existed during his enterprise years — built for the speed of Indian cloud adoption and the precision CISO boards now demand.





