Your security engineer opens the morning alert queue. 1,847 findings. Twelve critical, 340 high, the remainder trailing off into medium and low severity. She has three hours before standup, a patch window to coordinate, and a compliance audit next week. She makes a judgment call, triage by CVSS score, push the criticals to the development queue, mark the rest for next sprint review. It is the only rational response to an irrational volume of information.
What she does not know, “what no individual tool in your stack can tell her,” is that finding #847 on the medium-severity list and finding #1,203 on the high-severity list are not two separate problems. They are two steps in the same attack path. A misconfigured security group on a Kubernetes node, paired with an overly permissive service account that has never been reviewed, sitting adjacent to an unpatched container running a public-facing API. Individually, each is a management task. Together, they are a breach waiting for an attacker who has read the same CVE database your scanner uses.
The CNAPP correlation engine is the architectural component that would have flagged this combination as a single, critical, named attack path, not three separate findings, within seconds of the misconfiguration being introduced. It is the capability that separates a genuine cloud-native application protection platform from a dashboard that aggregates the same alerts you already have.
NASSCOM estimates that cloud workload deployment among Indian organizations grew at triple the global average rate between 2021 and 2023, the attack surface is expanding faster than any team can manually monitor. CERT-In‘s 6-hour breach reporting mandate has simultaneously compressed the acceptable detection window to a standard that point-solution alert queues structurally cannot meet. The correlation engine is not a feature. It is the answer to a specific operational crisis.
In this Guide, You Will Learn:
- What the CNAPP correlation engine is; and the precise architectural problem it solves
- How contextual risk analysis converts alert noise into actionable attack path intelligence
- The Attack Path Intelligence Model for evaluating correlation depth
- Three Indian enterprise scenarios where correlation changed the outcome
- Six strategic recommendations for security leaders ready to act
Cloud Alert Fatigue Is Not a People Problem. It Is an Architecture Problem.
Security teams are not failing because they lack skill or dedication. They are failing because the architecture they operate produces an unprocessable volume of decontextualized signals. The average enterprise cloud environment generates between 2,000 and 3,500 security findings per day. A team of eight analysts working eight-hour shifts could not meaningfully evaluate every finding. So they triage. And in triage, context collapses.
The IBM Cost of a Data Breach Report 2025 found that the global mean time to identify a breach stood at 204 days. The reason is structural: tools that detect individual events cannot identify the sequences that constitute breaches.
Did You Know?
A 2025 Enterprise Strategy Group study found that security analysts spend an average of 27% of their working hours managing and correlating findings across security tools, before investigating a single genuine threat. In a 10-person security team, that is the equivalent of 2.7 full-time analysts consumed entirely by tool management overhead. The CNAPP correlation engine is, among other things, an operational efficiency recovery mechanism.
The cloud-specific dimension of this problem is that cloud infrastructure changes continuously. A developer spins up a new EC2 instance during a feature deployment. A DevOps engineer modifies a security group rule to unblock a staging test. A CI/CD pipeline creates a new IAM role for a microservice. Each change potentially introduces a new configuration that, in combination with existing infrastructure, creates an exploitable path. The correlation question, does this change, in context, create a dangerous combination.
Expert Insight
The most dangerous finding in any cloud environment is rarely the one with the highest CVSS score. It is the one that connects a public entry point to a sensitive data asset through a chain of individually manageable risks. CVSS-based prioritization ignores this entirely, it evaluates each vulnerability in isolation, with no knowledge of the network context, the identity permissions, or the data sensitivity of the asset it affects. A CVSS 9.8 vulnerability on an air-gapped internal development server is less urgent than a CVSS 6.5 vulnerability on a publicly reachable container with an IAM role that grants production data lake access. Only a correlation engine can tell you which is which.
The bridge from this problem to its solution is not more tools, it is a different architecture. The correlation engine maps that architecture: the layer that finally allows your security intelligence to flow across domains and surface the combinations that actually matter.
Why Reducing Alert Volume Is the Wrong Goal and What to Optimize
Most CNAPP vendors sell correlation as an alert reduction play. “We’ll cut your alert volume by 80%.” Security leaders buy it. Then they discover the platform achieved that number by suppressing low-confidence findings nobody was processing anyway. The real attack paths are still there, just buried in a shorter list instead of a longer one.
Alert reduction is an output, not an objective. The right target is attack path visibility: the ability to see, with precision, the exact exploitable sequences connecting an external entry point to a sensitive asset. A platform surfacing 12 genuine, high-fidelity attack paths across 10,000 resources has achieved something fundamentally different from one that compressed 3,000 alerts into 300. One gives your team intelligence. The other gives them a tidier queue.
The same problem plagues CVSS-based prioritization. CVSS scores are calculated in a vacuum,they don’t know whether the vulnerable service is internet-exposed, whether the attached IAM principal is over-privileged, or whether the data within reach is regulated. A correlation engine that actually ingests this context will routinely flag a CVSS 5.5 as critical and deprioritize a CVSS 9.0 as low actual risk, because environment context changes everything.
| Old Approach | Better Approach |
|---|---|
| Prioritizing by CVSS score, sending 3,000 findings to developers ranked by severity | Prioritizing by attack path completeness, surfacing only findings that form exploitable chains from public exposure to sensitive data |
| Treating misconfiguration alerts and vulnerability alerts as separate workstreams managed by different teams | Correlating misconfiguration, identity, and vulnerability findings into unified attack path objects reviewed by a single team |
| Measuring security team effectiveness by findings closed per sprint | Measuring effectiveness by reduction in open attack paths from public internet to crown-jewel assets |
| Using SIEM for cloud security correlation, a tool designed for log analysis, not cloud asset relationship mapping | Using a native CNAPP correlation engine with a cloud asset graph that understands infrastructure relationships, not just event sequences |
| Running quarterly access reviews as a separate IAM governance exercise | Continuously correlating active identity permissions with adjacent infrastructure exposure as part of the same risk model |
“The security team that eliminates ten genuine attack paths has done more than the security team that closed a thousand findings. These are not the same achievement, and treating them as equivalent is how breaches happen in multi-tooled environments.”
The practical implication for DevSecOps teams is very specific. If a cloud security platform cannot show you the path from a public IP address through a specific vulnerability to a specific data asset, with the identity permissions that make the traversal possible, graphically, then it is not correlating. In fact this is commonly known as aggregating. Aggregation is a user interface decision, whereas correlation is an architectural capability. And you can see the difference in your mean time to detect, your CERT-In compliance posture, and eventually, in your breach history.
The Attack Path Intelligence Model: A Framework for Evaluating CNAPP Correlation Depth
If you’re evaluating a competency of correlation engine of a certain CNAPP platform, then you must do it through a structured lens. One such lens is, “Attack Path Intelligence Model.” It is a correlation maturity framework incorporated by Cy5 to systematically identify and prioritise real attack paths. It has four progressive capability levels that separate platforms like ion that correlate from platforms that merely collect.
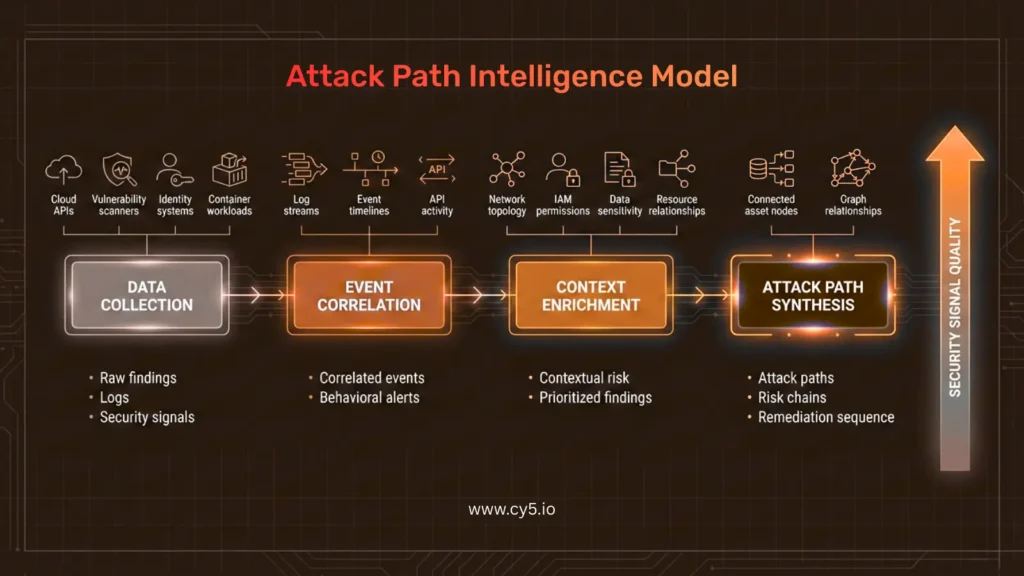
Level 1: Data Collection — The Necessary Foundation
At the first level, a platform ingests security-relevant events and findings from cloud APIs, vulnerability scanners, identity governance systems, and workload agents. Data collection is table stakes — every CNAPP vendor does this. The quality differentiator at this level is coverage breadth (how many cloud services, providers, and resource types are supported), ingestion latency (real-time event-driven vs. scheduled polling), and normalization fidelity (how accurately are findings from different sources translated into a common schema).
What good looks like: AWS CloudTrail events, Azure Active Directory logs, GCP Audit Logs, Kubernetes audit logs, and container image scan results, all flow into the same normalized data store within seconds of generation, not on the next scheduled polling cycle.
Common Mistake:
Accepting scheduled polling as equivalent to event-driven ingestion. A platform that polls AWS APIs every 4 hours has a 4-hour detection blind spot, the exact window attackers use to establish initial access, move laterally, and stage exfiltration. For CERT-In’s 6-hour reporting window, a 4-hour blind spot is not a performance gap. It is a compliance failure.
Level 2: Event Correlation; Connecting What Happened
At the second level, the platform begins connecting related events. For example, identifying that a CloudTrail API call and an IAM policy change along with a security group modification are related to the same resource, the same actor, or the same time window. This is the level at which a SIEM platform must operate in cloud environments: event sequence analysis with rule-based correlation. It is genuinely useful for detecting known attack patterns. It cannot detect novel combinations of configuration states that create exploitable conditions without a triggering event.
What good looks like: A sequence of API calls consistent with cloud reconnaissance; ‘DescribeInstances,’ ‘ListBuckets,’ ‘GetAccountAuthorizationDetails,’ from a credential outside of normal working hours is correlated into a single behavioral alert with attribution to a specific identity and a specific set of accessed resources.
Common Mistake:
Treating SIEM-based cloud event correlation as equivalent to CNAPP correlation. SIEM correlates events in time sequences. CNAPP correlates asset relationships in configuration space. The former catches attackers moving through your environment. The latter prevents the conditions that make movement possible in the first place. Both are necessary. Neither replaces the other.
An implementation note for Indian Companies:
Many Indian enterprises have made significant SIEM investments, often Splunk or IBM QRadar deployments, and are reluctant to position CNAPP as a replacement. The honest answer is that it is not: SIEM and CNAPP correlation are complementary capabilities addressing different temporal horizons. SIEM catches what is happening now. CNAPP correlation identifies what your environment makes possible, before an attacker tests it.
Level 3: Context Enrichment; Understanding What It Means
At the third level, the platform enriches each finding with the full environmental context that determines its actual risk level. This means overlaying network reachability (“Is the vulnerable resource publicly accessible?“), identity permissions (“what can an attacker do if they compromise this resource?“), data sensitivity (“what data is within reach?“), and business criticality (“is this a production workload?“). Context enrichment is where CVSS-based prioritization gets replaced by environment-specific risk scoring that reflects your actual exposure.
What good looks like: A medium-severity container vulnerability automatically inherits the risk context of its host cluster, including its network exposure, the permissions of its service account, and the sensitivity of the data stores it can reach, and is either promoted to critical attack path status or confirmed as a low-actual-risk finding, without analyst intervention.
Common Mistake:
Building context enrichment as a manual analyst step rather than an automated platform function. When context enrichment requires a human to cross-reference three different tools, it becomes the first step dropped during high-alert-volume periods, which is precisely when it matters most.
Do Give it a Read: How CNAPP Works in Multi-Cloud: The Unified Security Architecture
Level 4: Attack Path Synthesis, Seeing What Attackers See
At the fourth and most advanced level, the correlation engine synthesizes context-enriched findings into complete attack paths: directed graphs showing the specific sequence of conditions, from initial entry point to target asset, that constitute a viable breach scenario. Each attack path includes the specific misconfigurations, identity permissions, and vulnerabilities that enable traversal, ranked by the business impact of the target asset. This is the level at which correlation becomes genuinely predictive rather than descriptive.
What good looks like: “Public internet access → EC2 instance with CVE-2024-XXXX → IAM role with S3:GetObject on production-data-lake → 2.1M customer records” surfaces as a single, named, critical attack path with a specific remediation sequence: patch the CVE, restrict the IAM role, or remove the public access. Any one of these breaks the path.
Cy5’s ion Cloud Security platform operationalizes Level 4 through its contextual correlation engine, which builds a real-time graph of asset relationships across cloud accounts and uses it to identify the toxic combinations, specific chains of individually manageable risks that together constitute attack vectors. The platform surfaces these as named attack paths rather than finding aggregations, giving security teams the precise remediation sequence that breaks the chain with minimum operational disruption.
Common Mistake:
Conflating graph visualization with graph-based analysis. Several platforms display asset relationship graphs as a UI feature without using graph traversal algorithms to actually compute attack paths. The test: can the platform identify, programmatically, all paths from 0.0.0.0/0 to resources tagged as containing PII, without a human drawing the connections manually? If not, it is a visualization tool, not a correlation engine.
CNAPP Correlation in Indian Enterprise Environments: Three Scenarios
Scenario 1: The Fintech That Discovered a Three-Step Path to Customer Data
Context: A Bengaluru-based Series B payments fintech running its core transaction processing on AWS across three accounts had deployed a CSPM tool and a separate vulnerability scanner as its cloud security stack. Both tools were reporting findings daily.
The specific risk: Over a four-month period, three independent changes accumulated in one cloud account. A developer modified a security group to allow inbound traffic from 0.0.0.0/0 on port 8080 for a staging test, intending to revert it after the test. The revert never happened.
A separate CI/CD pipeline deployment created a new Lambda function with an execution role that had been copied from a production template, and inherited production-level S3 permissions. A third change, two weeks later, added a new S3 bucket with customer KYC documents, inadvertently tagged with a permissive bucket policy that the copied IAM role could access.
What each tool saw: The CSPM tool flagged the security group as a medium-severity misconfiguration. The vulnerability scanner had no visibility into the IAM role or the S3 bucket policy. Neither tool had any awareness of the other’s findings. No analyst connected the three events because they occurred across a four-month window and appeared in three separate alert queues.
What correlation would have changed: A correlation engine operating at Level 4 of the Attack Path Intelligence Model would have identified the complete chain within seconds of the third change: public network access → exposed Lambda → over-permissioned IAM role → sensitive S3 bucket with customer KYC data. This would have surfaced as a single critical attack path, triggering immediate remediation rather than sitting in three separate medium-priority queues. The fintech discovered the exposure during a RBI-mandated IT audit six months after the third change was introduced.
Scenario 2: A GCC Managing Global Standards and CERT-In Simultaneously
Context: A Hyderabad-based Global Capability Centre supporting a European financial services parent ran a hybrid cloud environment across Azure and AWS. The security team reported to both the India CISO and the global Group CISO, with different tooling mandated for each reporting line.
The specific risk: The GCC’s Azure environment had a specific misconfiguration pattern that neither tool flagged as critical: several Azure Virtual Machines running internal financial calculation services had been assigned Managed Identities with Contributor-level access to the entire subscription, a configuration that had been approved for initial setup convenience and never restricted. Separately, the same VMs had public-facing ports open for a legacy remote management tool that the parent company’s global IT team had flagged for decommissioning but had not yet removed.
What changed with correlation: When the GCC deployed a unified CNAPP platform with correlation capability, the attack path appeared immediately: public-facing legacy management port → VMs with subscription-level Contributor identity → lateral movement possible to all resources in subscription → parent company’s financial data. The global Group CISO, who had been receiving separate CSPM reports and separate vulnerability reports for 14 months, saw this combination for the first time. Remediation, restricting the Managed Identity scope and closing the legacy port, took four hours. The attack path had been open for over a year.
The CERT-In dimension: Under India’s 6-hour reporting mandate, had this path been exploited, the GCC would have been required to report within 6 hours of discovery. The correlation platform’s real-time attack path surfacing meant the discovery-to-reporting timeline was now measured in minutes rather than the days required to manually cross-reference two separate tool outputs.
Also Read: Cloud Security Best Practices for 2026
Six Recommendations for Security Leaders Evaluating CNAPP Correlation Capability
1. Test Correlation Depth Before Buying, Not After
The most reliable way to evaluate a CNAPP correlation engine is a structured proof-of-concept with a specific test scenario: introduce three related misconfigurations in a test environment, a public security group, an over-permissioned IAM role, and a sensitive data store, and measure whether the platform surfaces a single correlated attack path or three separate findings. If it generates three findings, it is aggregating. If it generates one attack path with a specific remediation sequence, it is correlating. Run this test on every platform you evaluate. The results are frequently surprising.
Signal that you have done this right: The platform’s output names the attack path, shows the traversal steps graphically, ranks it by the business impact of the target asset, and provides a specific remediation sequence that breaks the chain with minimum operational disruption.
2. Require Event-Driven Ingestion, Not Scheduled Polling
A correlation engine is only as current as its data. A platform that polls cloud APIs every 4 hours has a 4-hour blind spot between the introduction of a misconfiguration and its detection. In a dynamic cloud environment where developers are deploying continuously, this blind spot is not a theoretical concern, it is a routine operational gap. Event-driven ingestion, where configuration changes trigger immediate evaluation, is the architectural prerequisite for correlation that is relevant rather than historical.
CERT-In’s 6-hour breach reporting mandate is incompatible with 4-hour polling cycles. Indian enterprises subject to CERT-In obligations should treat event-driven ingestion as a compliance requirement, not a platform preference.
3. Integrate Correlation Output Directly into Your Development Workflow
Attack paths are created by infrastructure changes made in development pipelines. The most efficient point of remediation is the moment of creation, not the moment of detection in production. CNAPP correlation engines that integrate with CI/CD pipelines can evaluate infrastructure-as-code changes before deployment, identifying whether a proposed change would create or extend an attack path in the production environment. This shift-left capability reduces remediation cost by an order of magnitude compared to post-deployment detection.
Signal that you have done this right: A pull request that would create a public-facing security group adjacent to an over-permissioned IAM role is flagged in the CI/CD pipeline with a specific “would extend attack path” warning, before it reaches the production environment.
4. Map Correlation Findings to Your Regulatory Framework
CNAPP correlation output is most persuasive to auditors and regulators when it is mapped to specific regulatory control requirements. For Indian BFSI entities, this means mapping attack paths to RBI’s IT Governance Master Direction control domains. For organizations subject to DPDP Act obligations, it means identifying which attack paths reach personal data stores and ensuring those paths are prioritized for remediation. Platforms that automate this mapping, generating compliance posture reports that reflect correlated risk rather than raw finding counts — significantly reduce audit preparation overhead.
Signal that you have done this right: Your next CERT-In compliance report documents the number of exploitable attack paths to regulated data stores, the mean time to remediation for critical paths, and the continuous monitoring architecture that detected them, not the number of CSPM findings generated.
5. Use Correlation to Rationalize Your Tool Stack
One of the underappreciated operational benefits of a mature CNAPP correlation engine is that it makes visible the redundancies in your current tool stack. When a correlation engine ingests findings from your CSPM, your vulnerability scanner, your identity governance platform, and your CWPP tool and correlates them into attack paths, it also reveals which tools are contributing unique signal and which are generating noise that overlaps with other tools’ output. This analysis typically supports the business case for tool consolidation, reducing both license cost and analyst overhead.
Organizations that have consolidated to a unified CNAPP platform with native correlation, such as Cy5’s ion Cloud Security platform, report operational savings equivalent to 3 person-months per year in security operations overhead, alongside 85–96% reductions in alert noise. In Indian enterprise budget contexts where security team headcount is constrained, this efficiency recovery is often the decisive factor in procurement approval.
6. Build Your Board Report Around Attack Paths, Not Finding Counts
The most durable organizational change enabled by CNAPP correlation is a new language for reporting security posture to leadership. Attack paths are intuitively comprehensible to non-technical board members and CFOs in ways that finding counts and CVSS distributions are not. “We identified and remediated 14 attack paths from the public internet to customer data this quarter” communicates security effectiveness more clearly and more honestly than “we closed 1,847 findings at an 82% remediation rate.” Organizations that make this language shift find that board conversations about security investment become significantly more productive.
Signal that you have done this right: Your board security presentation includes a trend line of open attack paths to sensitive data assets, decreasing quarter over quarter, and a specific account of the highest-risk path identified and remediated in the period.
Where to Start?
A 3-step triage for teams feeling the alert fatigue now
- Step 1 (This Week)
Run the correlation test on your current platform. Introduce three related test misconfigurations in a non-production account and observe whether your platform generates one correlated attack path or three separate findings. This single test tells you more about your correlation capability than any vendor briefing.
- Step 2 (This Month)
Identify your five highest-priority attack path candidates. Manually cross-reference your last 30 days of CSPM, vulnerability, and identity governance findings. Look for any combination of public network access + IAM over-privilege + unpatched workload targeting the same resource cluster. These are the attack paths your current architecture is missing. Document them. They are your business case.
- Step 3 (This Quarter)
Run a structured CNAPP correlation POC. Define three success criteria before the POC begins, specific attack path detection, specific alert noise reduction, specific compliance mapping output. Evaluate every platform against the same criteria. Procurement decisions made without defined success criteria produce platforms that satisfy the vendor demo, not the operational requirement.
What the Research and Frameworks Say About Correlation-Based Cloud Security
The strategic direction of the security industry is unambiguously toward correlation-based, context-aware risk models, a movement validated by independent research, standards bodies, and regulatory frameworks simultaneously.
Gartner’s 2023 Innovation Insight for CNAPP specifically identified contextual correlation as the primary differentiating capability among CNAPP platforms, noting that organizations using platforms with genuine attack path analysis demonstrated materially better security outcomes than those using platforms that aggregated findings without correlation.
Gartner’s research further found that by 2025, organizations that consolidate security tooling under a unified CNAPP architecture will reduce security-related incidents by 45% compared to those maintaining point-solution stacks, a projection that has been tracking ahead of pace based on early adoption data.
MITRE ATT&CK for Cloud, the definitive taxonomy of cloud attack techniques maintained at attack.mitre.org, documents 13 primary tactics used against cloud environments. Analyzing the documented attack sequences reveals that 67% of successful cloud breaches in the MITRE dataset involved three or more tactics executed in sequence, meaning they were invisible to any single-tactic detection tool and only detectable through cross-tactic correlation. The CNAPP correlation engine is the architectural response to this specific finding.
The NIST Cybersecurity Framework 2.0, released in 2024, introduced specific guidance on continuous cloud security monitoring that explicitly references the need for integrated detection across cloud infrastructure, identity, and workload domains, the exact multi-domain correlation that CNAPP correlation engines provide. For Indian enterprises referencing NIST CSF as a security program baseline, this guidance creates a direct alignment between framework compliance and CNAPP correlation capability.
Expert Insight: The CIS Controls Alignment
CIS Controls v8 Implementation Group 2 and 3 both include specific controls for continuous vulnerability management, audit log management, and network monitoring that, read together, describe the input requirements for a CNAPP correlation engine. Organizations implementing CIS Controls IG2 or IG3 are already obligated to generate the data that correlation engines consume, they are simply not yet required to correlate it. The natural next step from CIS Controls compliance is CNAPP correlation deployment. The data infrastructure is already there.
Cy5 has operated at the intersection of Indian regulatory requirements and enterprise cloud security for almost five years. Under certain non-disclosure. they have documented deployments across BFSI, telecom, ed-tech, and GCC organizations in India, UK, Germany, Indonesia, and the UAE. The ion platform’s correlation engine was explicitly designed from first principles for the Indian operational context. Their threat detection is empowered by event-driven architecture for CERT-In compliance, prebuilt regulatory mapping for RBI and DPDP Act requirements, and hybrid ingest capability for organizations navigating the transition from on-premises to cloud infrastructure. Customer outcomes include 97% MTTD reduction in telecom deployments and 96% alert noise reduction in enterprise security operations contexts.
The Gap Between Detecting and Understanding Is Where Breaches Live
Every security tool in your current stack is detecting something real. The misconfigurations are real. The vulnerabilities are real. The identity risks are real. What can be said superficial or missing in your current architecture? It is the understanding that how those real findings connect to each other and what they cause together. That gap between detecting and understanding is exactly the space where attacker seeks opportunities for initial access and exfiltration. Statistically, is the 204-day mean detection time. It is always the kind of breach that your tools technically saw coming and your architecture structurally could not surface or relate.
The CNAPP correlation engine closes that gap. It does by generating a different quality of intelligence: named attack paths, specific traversal sequences, business-impact-ranked remediation priorities. It brings intelligence that a security engineer can act on immediately without spending long hours cross-referencing three separate tool dashboards. Intelligence that a CISO can present to a board as a trend line of risk reduction rather than a table of finding counts. Intelligence that satisfies a CERT-In auditor’s continuous monitoring requirement rather than a quarterly scan report.
FAQs: CNAPP Correlation Engine
A CNAPP correlation engine is the architectural component within a Cloud-Native Application Protection Platform that identifies relationships between security findings across multiple domains, cloud posture, identity, workload, and network, and synthesizes them into complete attack paths. Rather than generating individual alerts for each misconfiguration, vulnerability, or identity risk, the correlation engine surfaces the specific combinations of conditions that together constitute exploitable breach scenarios, ranked by the business impact of the assets at risk.
SIEM correlation analyzes event sequences in time, it detects that a series of log events occurring in a specific order matches a known attack pattern. CNAPP correlation analyzes asset relationships in configuration space, it detects that a specific combination of cloud infrastructure states (a public-facing resource, an over-permissioned identity, an unpatched workload) creates an exploitable path regardless of whether any attack event has occurred. SIEM catches attacks in progress. CNAPP correlation prevents the conditions that make attacks possible. Both are necessary; neither replaces the other.
Cloud attack path analysis is the process of identifying directed sequences of exploitable conditions, from an initial entry point to a target asset, in a cloud environment. An attack path might be: public network access → exploitable vulnerability on a container → service account with excessive IAM permissions → sensitive S3 bucket. Attack path analysis is the output of a CNAPP correlation engine operating at full capability and represents the highest-fidelity form of cloud security intelligence available — because it shows you what an attacker would do, not just what conditions exist.
CNAPP correlation reduces alert fatigue by replacing individual finding alerts with correlated attack path alerts. Instead of generating one alert per misconfiguration, vulnerability, or identity risk, which in a large enterprise cloud environment means thousands of daily alerts, the correlation engine evaluates whether individual findings are related and surfaces only the combinations that form exploitable chains. Organizations deploying CNAPP platforms with genuine correlation capability typically report 85–96% reductions in actionable alert volume, with the remaining alerts representing higher-fidelity, higher-urgency findings than the original noise floor.
Contextual risk analysis is the process of evaluating a security finding not in isolation, but in the context of the full environment surrounding the affected resource. This includes network reachability (is the resource publicly accessible?), identity permissions (what can an attacker do if they compromise this resource?), adjacent vulnerabilities (are there other exploitable conditions nearby?), and data sensitivity (what is the business impact of this asset?). Contextual risk analysis routinely reclassifies findings, promoting low-CVSS vulnerabilities on highly exposed, over-permissioned, business-critical workloads to critical priority, and deprioritizing high-CVSS vulnerabilities on isolated, low-impact resources.
CERT-In’s 6-hour breach reporting mandate requires Indian organizations to detect incidents within a window that traditional scheduled-scan tools cannot support. CNAPP correlation engines with event-driven architecture detect attack paths the moment a configuration change creates them, not on the next scheduled polling cycle, which is the operational prerequisite for 6-hour reporting compliance. Additionally, CNAPP platforms with prebuilt CERT-In compliance mapping can automatically assess which attack paths involve regulated data or systems, generating the evidence trail that CERT-In inspection teams require. For BFSI entities simultaneously subject to RBI monitoring obligations, the same correlation output maps to multiple regulatory frameworks from a single platform.
Alert aggregation collects findings from multiple tools into a common interface, a single dashboard showing CSPM alerts, vulnerability scanner output, and identity governance flags in one view. CNAPP correlation goes further: it analyzes the relationships between findings from different tools and identifies whether they are steps in the same attack path. The practical test is straightforward: does the platform surface a single, named attack path connecting a public-facing resource to a sensitive data store through a chain of misconfigurations and identity risks? Or does it display three separate findings that a human analyst must manually connect? If the latter, it is aggregating, not correlating.
In Kubernetes environments, attack path analysis evaluates the specific combination of cluster misconfiguration, container vulnerability, network policy, and service account permissions that together create exploitable paths. A typical Kubernetes attack path might be: exposed API server port → container with privilege escalation vulnerability → pod running with cluster-admin service account → lateral movement to other workloads or cloud resources. CNAPP correlation in Kubernetes environments requires the platform to understand both the Kubernetes-specific security model, RBAC, network policies, pod security standards, and the relationship between the Kubernetes cluster and the underlying cloud infrastructure and identity systems.
An effective CNAPP correlation engine requires four data streams: cloud infrastructure configuration state (from cloud provider APIs, AWS Config, Azure Resource Graph, GCP Asset Inventory); identity and permission data (IAM roles, policies, entitlements, and usage patterns); workload and vulnerability data (container image scans, CVE databases, runtime agent telemetry); and network topology data (security groups, VPC configurations, load balancer rules, firewall policies). The quality of correlation output is directly proportional to the completeness and freshness of these four streams — which is why event-driven ingestion is architecturally preferable to scheduled polling.
Indian enterprises evaluating CNAPP correlation platforms should apply four specific criteria beyond the standard feature checklist. First, India regulatory alignment: does the platform have prebuilt compliance packs for CERT-In guidelines, DPDP Act data classification controls, and RBI/SEBI framework mapping? Second, hybrid ingest capability: can it handle both cloud-native event streams and on-premises syslog sources for organizations mid-migration? Third, event-driven architecture: does it evaluate misconfigurations in real time or on scheduled cycles? Fourth, attack path quality: does a structured POC produce genuine attack paths or aggregated findings?
Cy5’s ion platform was designed with India-first regulatory alignment as a core capability, a differentiation that global CNAPP platforms with retrofitted India compliance modules have found difficult to match operationally.
Graph-based security analysis is the use of graph database technology to model cloud environments as networks of related assets, nodes representing resources, identities, and data stores; edges representing permissions, network connections, and dependencies. A CNAPP platform using graph-based analysis can run graph traversal queries to identify all paths between any two nodes, for example, all paths from a public IP address to a resource tagged as containing PII. This approach is architecturally superior to rule-based correlation because it can identify novel attack paths that no predefined rule anticipated, as long as the exploitable relationships are represented in the graph.
CNAPP correlation supports DevSecOps teams by integrating attack path intelligence directly into the development workflow. In CI/CD pipeline integration, infrastructure-as-code changes are evaluated before deployment to determine whether they would create or extend attack paths in the production environment, shifting remediation to the point of creation rather than the point of detection. In developer ticketing integration, correlated attack path findings are converted into actionable Jira or ServiceNow tickets with the specific misconfiguration, the affected resources, the attack path it enables, and the specific fix that breaks the chain, without requiring developers to interpret raw security scanner output.
CNAPP correlation is operationally valuable for any organization with more than one cloud account, more than one workload type, and more than three security findings per day, which describes most cloud-using SMEs. For smaller organizations, the primary benefit is different from large enterprises: rather than alert volume reduction, the value is attack path visibility that prevents the accumulation of the misconfiguration and identity debt that becomes extremely expensive to remediate at scale. Many Indian Series A and Series B companies have deployed CNAPP correlation platforms and found that the architecture gap between their security assumptions and their actual exposure was significantly larger than anticipated.
CNAPP correlation and Zero Trust are mutually reinforcing architectures. Zero Trust establishes the principle that no identity or network location should be inherently trusted, all access should be continuously verified. CNAPP correlation provides the visibility layer that makes Zero Trust enforcement decisions intelligent: the correlation engine identifies which identities hold what permissions and whether those permissions, in combination with network exposure and workload vulnerabilities, create exploitable paths. Zero Trust without correlation visibility lacks the intelligence to know which access decisions are highest risk. Correlation without Zero Trust enforcement lacks the ability to act on what it finds.
CNAPP risk scoring assigns a composite risk score to each finding or attack path based on multiple contextual factors: the severity of the underlying vulnerability or misconfiguration (CVSS score as a starting point), the network reachability of the affected resource (publicly accessible vs. internal), the permissions of associated identities (over-privileged vs. least-privilege), the business criticality of the affected asset (production vs. development), and the sensitivity of accessible data (PII, financial records, regulated data vs. generic). A well-implemented CNAPP risk score is environment-specific, the same CVE on two different resources in the same organization can have radically different risk scores based on these contextual factors.
Key Takeaways
- The CNAPP correlation engine is not an alert reduction feature, it is an architectural capability that synthesizes findings from cloud posture, identity, workload, and network domains into complete, named attack paths.
- Alert aggregation and alert correlation are not the same thing. Aggregation creates a shorter list. Correlation creates a different quality of intelligence, one that shows attack sequences rather than individual findings.
- The Attack Path Intelligence Model, four levels from Data Collection through Event Correlation, Context Enrichment, and Attack Path Synthesis, provides a practical framework for evaluating genuine correlation depth in any CNAPP platform.
- CERT-In’s 6-hour reporting mandate requires event-driven correlation architecture. Scheduled polling creates detection blind spots that are incompatible with Indian regulatory compliance requirements.
- CVSS-based prioritization is structurally inadequate for cloud environments. A CVSS 5.5 finding on a publicly exposed, over-permissioned workload is more urgent than a CVSS 9.0 finding on an isolated development server, and only a correlation engine can tell you which is which.
- The test of correlation capability is simple: introduce three related misconfigurations in a test environment and measure whether the platform generates one attack path or three separate findings. Apply this test before any procurement decision.
- Indian enterprise security leaders should evaluate CNAPP correlation platforms specifically for India regulatory alignment, CERT-In, DPDP Act, RBI/SEBI framework mapping, as this capability is not uniformly present in global platforms.
About the Author

Kumar Shantanu specializes in translating complex cloud security architecture, CNAPP strategy, and multi-cloud risk management concepts into executive-ready insights for CISOs, DevSecOps leaders, and enterprise security teams. At Cy5.io, he develops research-driven thought leadership content focused on attack path analysis, cloud identity risk, compliance automation, and modern cloud security transformation.